ALWAYS_SANDBOX_DISPLAY_APIS
Change ID: 185004937
Default State: Disabled for all apps.
When enabled, applies Display API sandboxing to a package
regardless of windowing mode. The Display APIs will always provide
the app bounds.
To learn more about this change, see the section in the Android 12
behavior changes page about
Display methods that were deprecated.
|
AUTOFILL_NON_TEXT_REQUIRES_ON_RECEIVE_CONTENT_LISTENER
Change ID: 163400105
Default State: Enabled for apps that target Android 12 (API level 32) or higher.
Starting in Android 12, the platform can provide non-text suggestions (such as images) using the augmented autofill
framework (see autofill services). In order for an app to be able to handle these suggestions,
it must normally implement the OnReceiveContentListener API.
To make the adoption of this API smoother for apps that have previously implemented the
InputConnection.commitContent(InputContentInfo, int, Bundle)
API, we reuse that API as a fallback if OnReceiveContentListener is not yet implemented by the app. This fallback is only enabled on
Android 12 (API level 31). This change ID disables the fallback, such that apps targeting Android 12 (API level 32) and above must implement the
OnReceiveContentListener API in order to accept non-text suggestions.
|
BLOCK_FLAG_SLIPPERY
Change ID: 157929241
Default State: Enabled for all apps.
For apps running on Android 12 (API level 31), checks if
FLAG_SLIPPERY
is being used with any windows in the app. We expect that this flag is likely only used by the system components as it is an
unsupported field. If so, it will be restricted.
|
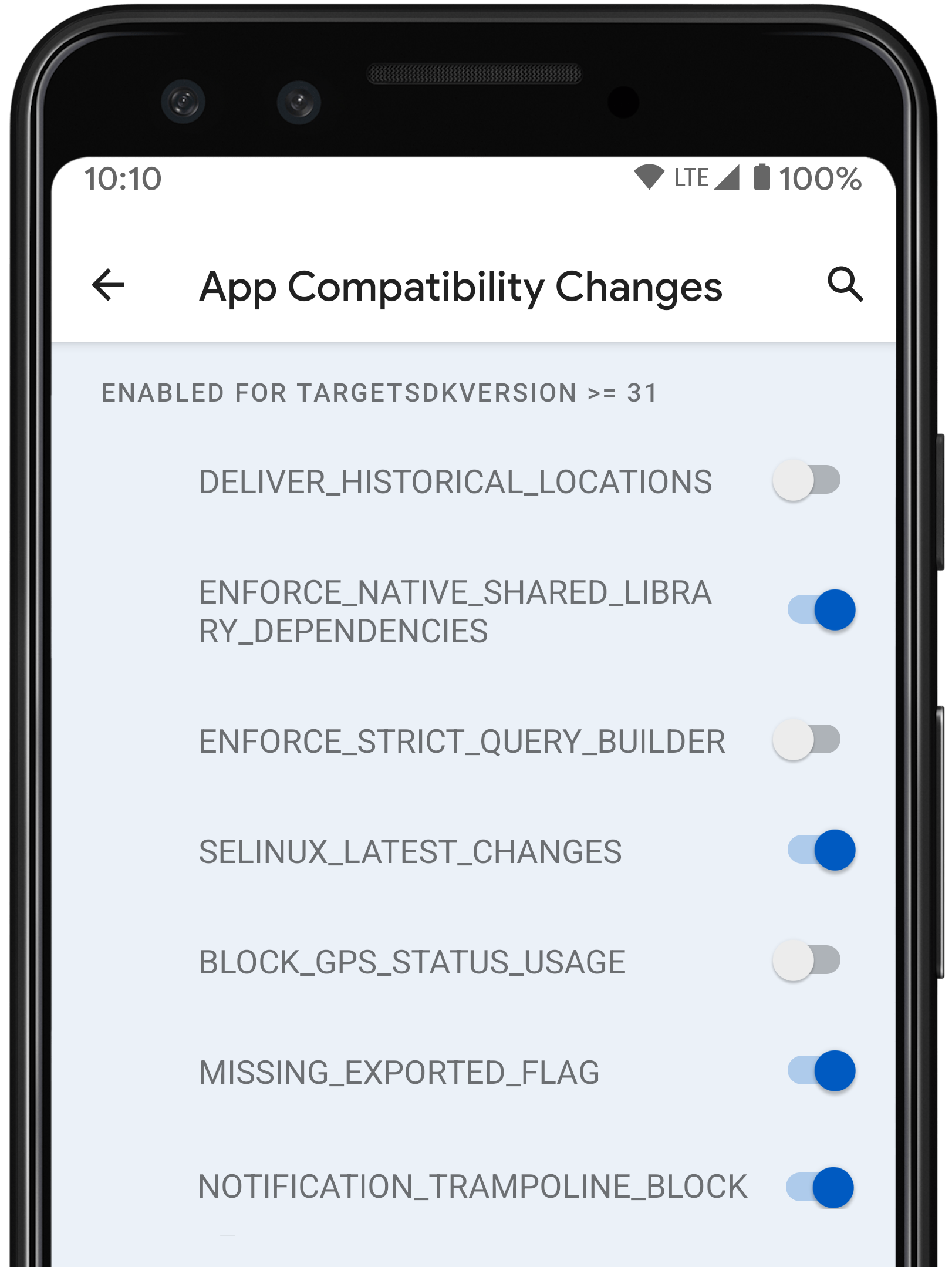
BLOCK_GPS_STATUS_USAGE
Change ID: 144027538
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, all GpsStatus
API usage must be replaced with GnssStatus APIs.
|
BLOCK_IMMUTABLE_PENDING_INTENTS
Change ID: 171317480
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, immutable PendingIntent
objects that are passed into location APIs will generate an IllegalArgumentException.
|
BLOCK_PENDING_INTENT_SYSTEM_API_USAGE
Change ID: 169887240
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, LocationRequest system APIs can't be used with PendingIntent
location requests.
|
BLOCK_UNTRUSTED_TOUCHES
Change ID: 158002302
Default State: Enabled for all apps.
To preserve system security and a good user experience, Android 12 prevents apps from consuming touch events
where an overlay blocks the app in an unsafe way.
To learn more about this change, see Untrusted touch events are blocked.
|
CALL_ACTIVITY_RESULT_BEFORE_RESUME
Change ID: 78294732
Default State: Enabled for apps that target Android 12 (API level 32) or higher.
For apps targeting Android 12 (API level 32) and higher, corrects the lifecycle of activity result to guarantee that an activity gets
the activity result just before resume.
|
CAMERA_MIC_INDICATORS_NOT_PRESENT
Change ID: 162547999
Default State: Disabled for all apps.
Indicates that this device supports camera and microphone indicators. Will be false if
present, because the CompatChanges#isChangeEnabled
method returns true if the Change ID is not present.
|
CANNOT_INSTALL_WITH_BAD_PERMISSION_GROUPS
Change ID: 146211400
Default State: Enabled for apps that target Android 12 (API level 32) or higher.
For apps targeting Android 12 (API level 32) and higher, the package manager will not install a package if there are malformed permission groups.
Permission groups should only be shared between apps sharing a certificate. If a permission belongs to a group, that group must also be defined.
|
CHANGE_ID_AUTH_STATE_DENIED
Change ID: 181350407
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For client apps targeting Android 12 (API level 31) and higher, a SecurityException is thrown when they are in the denied
authorization state and attempt to send a message to a nanoapp.
|
CHANGE_ID_SAMPLING_RATE_SENSORS_PERMISSION
Change ID: 136069189
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, a SecurityException is thrown when they do not have
HIGH_SAMPLING_RATE_SENSORS permission, run in debug mode, and request sampling rates that are faster than 200 Hz.
|
DELIVER_HISTORICAL_LOCATIONS
Change ID: 73144566
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, location clients may receive historical locations (from before the
present time) under some circumstances.
|
DISPLAY_INFO_NR_ADVANCED_SUPPORTED
Change ID: 181658987
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, provides backward compatibility for changes in TelephonyDisplayInfo.
|
DISPLAY_MODE_RETURNS_PHYSICAL_REFRESH_RATE
Change ID: 170503758
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, the platform might throttle down an app's frame rate to a divisor of the
refresh rate if it is more preferable (for example, if the app called to Surface.setFrameRate(float, int)).
Apps will experience Choreographer.postFrameCallback(Choreographer.FrameCallback)
callbacks and backpressure at the throttled frame rate. Apps use Display.getRefreshRate() and
Display.Mode.getRefreshRate() to know what the display refresh rate is.
Display.getRefreshRate() will always return the application frame rate and not the physical display refresh rate to allow
apps to do frame pacing correctly. Display.Mode.getRefreshRate() will return the app frame rate if compiled to a previous
release and starting with Android 12 (API level 31) it will return the physical display refresh rate.
|
DOWNSCALED
Change ID: 168419799
Default State: Disabled for all apps.
This change is the gatekeeper of all per-app buffer downscaling
changes. Enabling this change allows the following scaling factors to
be applied:
When this change is enabled for an app package, the app is forcibly
resized to the highest, enabled scaling factor. For example, 80% is
used if both 80% and 70%
(DOWNSCALE_80 and
DOWNSCALE_70) are
enabled.
|
DOWNSCALE_30
Change ID: 189970040
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 30% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_35
Change ID: 189969749
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 35% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_40
Change ID: 189970038
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 40% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_45
Change ID: 189969782
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 45% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_50
Change ID: 176926741
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 50% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_55
Change ID: 189970036
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 55% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_60
Change ID: 176926771
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 60% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_65
Change ID: 189969744
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 65% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_70
Change ID: 176926829
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 70% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_75
Change ID: 189969779
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 75% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_80
Change ID: 176926753
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 80% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_85
Change ID: 189969734
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 85% of the vertical and horizontal
resolution of the real display.
|
DOWNSCALE_90
Change ID: 182811243
Default State: Disabled for all apps.
When DOWNSCALED is also
enabled, enabling this change for a package forces the app to assume
it's running on a display with 90% of the vertical and horizontal
resolution of the real display.
|
DO_NOT_DOWNSCALE_TO_1080P_ON_TV
Change ID: 157629738
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Android TV apps targeting Android 12 (API level 31) and higher are expected to handle any Window size, including Window sizes greater than 1080p.
Apps that target earlier versions of Android do not expect to receive Windows larger than 1080p, so their Windows are downscaled to 1080p when necessary.
|
DROP_CLOSE_SYSTEM_DIALOGS
Change ID: 174664120
Default State: Enabled for all apps.
To improve user control when interacting with apps and the system, the ACTION_CLOSE_SYSTEM_DIALOGS
intent action is deprecated as of Android 12.
To learn more about this change, see Apps can't close system dialogs.
|
ENABLE_CHECKS_FOR_PRIVATE_FILES
Change ID: 172100307
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Apps targeting Android 12 (API level 31) and higher can't insert or update private files using media provider.
|
ENABLE_DEFERRED_SCAN
Change ID: 180326732
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Enable this option to defer the scan that is triggered as part of MediaProvider#update().
|
ENABLE_GET_CALL_STATE_PERMISSION_PROTECTION
Change ID: 157233955
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, enables READ_PHONE_STATE protection on APIs querying and notifying call state, such as TelecomManager#getCallState,
TelephonyManager.getCallStateForSubscription(), and
TelephonyCallback.CallStateListener.
|
ENABLE_GET_PHONE_ACCOUNT_PERMISSION_PROTECTION
Change ID: 183407956
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, enables READ_PHONE_NUMBERS or READ_PRIVILEGED_PHONE_STATE
protections on getPhoneAccount(PhoneAccountHandle).
|
ENABLE_INCLUDE_ALL_VOLUMES
Change ID: 182734110
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Enable this option to include database rows of files from a recently unmounted volume in MediaProvider#query.
|
ENABLE_RAW_MANAGE_EXTERNAL_STORAGE_ACCESS
Change ID: 178209446
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Enable this option to allow apps holding the Manifest.permission.MANAGE_EXTERNAL_STORAGE
permission to request raw external storage access.
|
ENFORCE_MINIMUM_WINDOW_ON_INEXACT_ALARMS
Change ID: 185199076
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, all inexact alarms are required to have a minimum window size, expected to be on the order of a few minutes. Practically, any alarms requiring
smaller windows are the same as exact alarms and should use the corresponding APIs provided, such as
setExact(int, long, PendingIntent). Inexact alarm with shorter windows specified
will have their windows elongated by the system.
|
ENFORCE_NATIVE_SHARED_LIBRARY_DEPENDENCIES
Change ID: 142191088
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Apps targeting Android 12 (API level 31) and higher need to declare dependencies to the public native shared libraries that
are defined by the device maker using uses-native-library tag in its AndroidManifest.xml. If any of the dependencies
can't be satisfied—for example, one of the dependencies doesn't exist—the package manager won't install the app. The dependency can be
specified as optional using the android:required attribute in the tag, in which case failing to satisfy the dependency won't stop
the installation.
Once installed, an app is provided with only the native shared libraries that are specified in the app manifest. Calling dlopen on
a native shared library that doesn't appear in the app manifest will fail even if it actually exists on the device.
|
ENFORCE_STRICT_QUERY_BUILDER
Change ID: 143231523
Default State: Disabled for all apps.
When enabled, the SQLiteQueryBuilder
verifies all CalendarProvider2 query selections against malicious arguments.
|
FGS_BG_START_RESTRICTION_CHANGE_ID
Change ID: 170668199
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, restricts when apps can start foreground services while running in the background.
|
FGS_START_EXCEPTION_CHANGE_ID
Change ID: 174041399
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, enables the system to throw an IllegalStateException if an app attempts to start a foreground service while running in the background.
|
Change ID: 156215187
Default State: Disabled for all apps.
For apps targeting Android 12 (API level 31) and higher, finish the InputConnection when the device becomes
non-interactive.
If enabled by the current input method, the current input connection will be
finished whenever the devices becomes non-interactive.
If not enabled, the current input connection will instead be silently deactivated when the devices becomes non-interactive, and an
onFinishInput() and
onStartInput()
pair is dispatched when the device becomes interactive again.
|
FORCE_DISABLE_HEVC_SUPPORT
Change ID: 174227820
Default State: Disabled for all apps.
Force disable an app from supporting the HEVC media capability.
Apps should declare their supported media capabilities in their
manifest but this flag can be used to force an app into not
supporting HEVC, hence forcing transcoding while accessing media
encoded in HEVC. Setting this flag overrides any OS level defaults
for apps. It is disabled by default, meaning that the OS defaults
take precedence. If both this flag and
FORCE_ENABLE_HEVC_SUPPORT are enabled, the OS ignores
both flags.
|
FORCE_ENABLE_HEVC_SUPPORT
Change ID: 174228127
Default State: Disabled for all apps.
Force enable an app to support the HEVC media capability Apps
should declare their supported media capabilities in their manifest
but this flag can be used to force an app into supporting HEVC, hence
avoiding transcoding while accessing media encoded in HEVC. Setting
this flag overrides any OS level defaults for apps. It is disabled by
default, meaning that the OS defaults would take precedence. If both
this flag and FORCE_DISABLE_HEVC_SUPPORT are enabled,
the OS ignores both flags.
|
FORCE_NON_RESIZE_APP
Change ID: 181136395
Default State: Disabled for all apps.
Forces the packages it is applied to to be non-resizable.
|
FORCE_RESIZE_APP
Change ID: 174042936
Default State: Disabled for all apps.
Forces the packages it is applied to to be resizable. We only
allow resizing in fullscreen windowing mode, but not forcing the app
into resizable multi-windowing mode.
|
HIDE_PROP_ICUBINARY_DATA_PATH
Change ID: 171979766
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, removes access to the android.icu.impl.ICUBinary.dataPath property.
|
IGNORE_ALLOW_BACKUP_IN_D2D
Change ID: 183147249
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, android:allowBackup is ignored for apps during device-to-device (D2D) migrations.
|
IGNORE_FULL_BACKUP_CONTENT_IN_D2D
Change ID: 180523564
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, include and exclude rules specified using android:fullBackupContent are ignored during device-to-device (D2D) transfers.
|
IME_AUTOFILL_DEFAULT_SUPPORTED_LOCALES_IS_EMPTY
Change ID: 169273070
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, getSupportedLocales() now returns
an empty locale list when it's not set, instead of the default system locale.
|
IS_BACKUP_SERVICE_ACTIVE_ENFORCE_PERMISSION_IN_SERVICE
Change ID: 158482162
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, the BACKUP permission needed for
isBackupServiceActive() is enforced on the service-side rather than client-side in BackupManager.
|
KEYSTORE_OPERATION_CREATION_MAY_FAIL
Change ID: 169897160
Default State: Disabled for all apps.
When enabled, keystore operation creation might fail according to
the new pruning strategy. Keystore used to work under the assumption
that the creation of cryptographic operations always succeeds.
However, the KeyMint backend has only a limited number of operation
slots.
In order to keep up the appearance of "infinite" operation slots,
the Keystore daemon would prune least recently used operations if
there was no available operation slot. As a result, good operations
could be terminated prematurely. This opened up AndroidKeystore up to
denial-of-service (DoS) and unintended livelock. For example, if
multiple apps woke up at the same time due to power management
optimizations and attempted to perform crypto operations, they start
terminating each others operations without making any progress.
To break out of livelocks and to discourage DoS attempts, we have
changed the pruning strategy for such that it prefers clients that
use few operation slots briefly. As a result, single operations that
don't linger inactive for more than 5 seconds will almost always
conclude unhampered by the pruning strategy. There are still some
operations related to file system encryption that can prune even
these operations, but those cases are extremely rare. As a side
effect of this new pruning strategy operation, creation can now fail
if the client has a lower pruning power than all of the existing
operations.
Pruning strategy: To find a suitable candidate,
we compute the malus for the caller and each existing operation. The
malus is the inverse of the pruning power (caller) or pruning
resistance (existing operation). For the caller to be able to prune
an operation, it must find an operation with a malus higher than its
own. For more details on the pruning strategy, see the implementation
of
operation.rs.
On Android 11 (API level 30) and lower, KeyStore2 will poll the
Keystore daemon for a free operation slot. For apps targeting
Android 11 (API level 30) and lower, it will still look like cipher and
signature object initialization always succeeds—however, it may take
longer to get an operation. All Android versions benefit from fairer
operation slot scheduling and a better chance to successfully conclude
an operation.
|
LOCK_DOWN_CLOSE_SYSTEM_DIALOGS
Change ID: 174664365
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, the Intent.ACTION_CLOSE_SYSTEM_DIALOGS can't be sent
unless the app also has the android.permission.BROADCAST_CLOSE_SYSTEM_DIALOGS permission. Note that this is the more restrictive version of #DROP_CLOSE_SYSTEM_DIALOGS
that expects the app to stop sending the Intent.ACTION_CLOSE_SYSTEM_DIALOGS intent once the app starts targets Android 12 (API level 31) or higher.
|
LOCK_DOWN_COLLAPSE_STATUS_BAR
Change ID: 173031413
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, the Manifest.permission.STATUS_BAR permission is required to collapse the
status bar panels due to security reasons. This was being exploited by malware to prevent the user from accessing critical notifications.
|
LOW_POWER_EXCEPTIONS
Change ID: 168936375
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, all LocationRequest objects marked as low power throw
exceptions if the caller does not have the LOCATION_HARDWARE permission, instead of silently dropping the low
power part of the request.
|
MISSING_EXPORTED_FLAG
Change ID: 150232615
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, an explicit value must be specified for the
android:exported attribute whenever an intent filter is defined.
To learn more about this change, see Safer exporting of components.
|
NATIVE_HEAP_POINTER_TAGGING_APP_ZYGOTE
Change ID: 207557677
Default State: Enabled for apps that target Android 12 (API level 32) or higher.
For apps targeting Android 12 (API level 32) and higher, native heap allocations in AppZygote process and its descendants
use a non-zero tag in the most significant byte.
To learn more about this change, see Tagged Pointers.
|
NATIVE_HEAP_ZERO_INIT
Change ID: 178038272
Default State: Disabled for all apps.
Enable automatic zero-initialization of native heap memory allocations.
|
NATIVE_MEMTAG_ASYNC
Change ID: 135772972
Default State: Disabled for all apps.
Enable asynchronous (ASYNC) memory tag checking in this process. This flag only affects hardware supporting the ARM
Memory Tagging Extension (MTE).
|
NATIVE_MEMTAG_SYNC
Change ID: 177438394
Default State: Disabled for all apps.
Enables synchronous (SYNC) memory tag checking in this process. This flag only affects hardware supporting the ARM
Memory Tagging Extension (MTE). If both NATIVE_MEMTAG_ASYNC and this option are enabled, this option takes
precedence and MTE is enabled in SYNC mode.
|
NEVER_SANDBOX_DISPLAY_APIS
Change ID: 184838306
Default State: Disabled for all apps.
When enabled, prevents Display API sandboxing from applying to a
letterbox or SCM activity. The Display APIs will continue to provide
DisplayArea bounds.
To learn more about this change, see the section in the Android
12 behavior changes page about
Display methods that were deprecated.
|
NOTIFICATION_CANCELLATION_REASONS
Change ID: 175319604
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Allows notification listeners to understand new cancellation reasons that are more specific.
|
NOTIFICATION_TRAMPOLINE_BLOCK
Change ID: 167676448
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
To improve app performance and UX, apps that target Android 12 cannot use services or broadcast receivers
as notification trampolines.
To learn more about this change, see Notification trampolines cannot be created from services or broadcast receivers.
|
NULL_TELEPHONY_THROW_NO_CB
Change ID: 182185642
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Used for checking if the target SDK version for the current process is Android 12 (API level 31) or higher.
Applies to the following methods:
|
OVERRIDE_MIN_ASPECT_RATIO
Change ID: 174042980
Default State: Disabled for all apps.
This change is the gatekeeper of all changes that force a given minimum aspect ratio. Enabling this change allows the following minimum aspect
ratios to be applied:
When this change is enabled for an app package, the minimum aspect ratio given in the app's manifest is overridden to the largest enabled
aspect ratio unless the app's manifest value is higher.
|
OVERRIDE_MIN_ASPECT_RATIO_LARGE
Change ID: 180326787
Default State: Disabled for all apps.
When OVERRIDE_MIN_ASPECT_RATIO is also enabled, enabling this change for a package sets
the activity's minimum aspect ratio to a large value as defined by OVERRIDE_MIN_ASPECT_RATIO_LARGE_VALUE.
|
OVERRIDE_MIN_ASPECT_RATIO_MEDIUM
Change ID: 180326845
Default State: Disabled for all apps.
When OVERRIDE_MIN_ASPECT_RATIO is also enabled, enabling this change for a package sets
the activity's minimum aspect ratio to a medium value as defined by OVERRIDE_MIN_ASPECT_RATIO_MEDIUM_VALUE.
|
PENDING_INTENT_EXPLICIT_MUTABILITY_REQUIRED
Change ID: 160794467
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, you must specify the mutability of each PendingIntent
object that your app creates. This additional requirement improves your app's security.
To learn more about this change, see Pending intents must declare mutability.
|
PREVENT_SETTING_PASSWORD_QUALITY_ON_PARENT
Change ID: 165573442
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
Admin apps targeting Android 12 (API level 31) and higher can't use DevicePolicyManager.setPasswordQuality(ComponentName, int)
to set password quality on the DevicePolicyManager instance obtained by calling DevicePolicyManager.getParentProfileInstance(ComponentName).
Instead, they should use DevicePolicyManager.setRequiredPasswordComplexity(int) to set
coarse-grained password requirements device-wide.
|
RATE_LIMIT_TOASTS
Change ID: 174840628
Default State: This change can't be toggled. It is only logged by the compatibility framework.
Enables rate limiting on the number of
Toast.show()
calls to prevent overburdening the user with too many toasts in a
limited time. Any attempt to show more toasts than allowed in a
certain timeframe results in the toast being discarded.
|
REQUIRE_EXACT_ALARM_PERMISSION
Change ID: 171306433
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, apps must have the Manifest.permission.SCHEDULE_EXACT_ALARM
permission in order to use any APIs for setting exact alarms, such as setExactAndAllowWhileIdle(int, long, PendingIntent)
and setAlarmClock(AlarmClockInfo, PendingIntent).
|
REQUIRE_READ_PHONE_STATE_PERMISSION_FOR_ACTIVE_DATA_SUB_ID
Change ID: 182478738
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, apps must have the Manifest.permission.READ_PHONE_STATE permission in
order to call TelephonyCallback.ActiveDataSubscriptionIdListener.
|
REQUIRE_READ_PHONE_STATE_PERMISSION_FOR_CELL_INFO
Change ID: 184323934
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, apps must have the Manifest.permission.READ_PHONE_STATE permission in
order to call TelephonyCallback.CellInfoListener.
|
REQUIRE_READ_PHONE_STATE_PERMISSION_FOR_DISPLAY_INFO
Change ID: 183164979
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, apps must have the Manifest.permission.READ_PHONE_STATE permission in
order to call TelephonyCallback.DisplayInfoListener.
|
RESTRICT_ADB_BACKUP
Change ID: 171032338
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, adb backup is automatically turned on for apps running as debuggable (android:debuggable set to true) and
unavailable to any other apps.
|
RESTRICT_DOMAINS
Change ID: 175408749
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, the updated form of the app links verification API is required. This requirement means an app must declare domains inside an intent filter that
includes all of the following:
android:autoVerify="true"Intent.ACTION_VIEWIntent.CATEGORY_BROWSABLEIntet.CATEGORY_DEFAULT- Only
IntentFilter.SCHEME_HTTP and/or IntentFilter.SCHEME_HTTPS, with no other schemes
On prior versions of Android, Intent.CATEGORY_BROWSABLE was not a requirement, other schemes were allowed, and setting autoVerify to true in any intent filter would
implicitly pretend that all intent filters were set to autoVerify="true".
|
SECURITY_EXCEPTION_ON_INVALID_ATTRIBUTION_TAG_CHANGE
Change ID: 151105954
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, enforces that all attributionTags sent to noteOp(String, int, String),
noteProxyOp(String, String),
and startOp(String, int, String)
are defined in the manifest of the package that is specified as a parameter of the methods.
To enable this change, both the package calling noteOp(String, int, String)
as well as the package specified as a parameter of the method must have this change enabled.
|
SELINUX_LATEST_CHANGES
Change ID: 143539591
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, opts in to the latest SELinux changes. Turning this change off for an app targeting
Android 12 (API level 31) or higher is a no-op. Has no effect for apps that use a shared user id.
|
SETTINGS_API_V2
Change ID: 178111421
Default State: Enabled for all apps.
The new user preference API for verifying domains marked autoVerify=true in AndroidManifest.xml intent filters is not yet implemented in
the current platform preview. For now, it is possible to preview the new user preference changes by enabling this ChangeId and using the
adb shell pm set-app-links-user-selection and similar commands.
|
USE_SHORT_FGS_USAGE_INTERACTION_TIME
Change ID: 183972877
Default State: Enabled for apps that target Android 12 (API level 31) or higher.
For apps targeting Android 12 (API level 31) and higher, determines whether to use a shorter timeout before elevating the standby bucket to
ACTIVE when apps start a foreground service.
|