Identidade
A segurança e a funcionalidade do seu app Android dependem do gerenciamento de identidade do usuário. Isso envolve verificar quem são seus usuários (autenticação), controlar o acesso aos dados dos usuários (autorização) e oferecer um processo de criação de conta tranquilo.
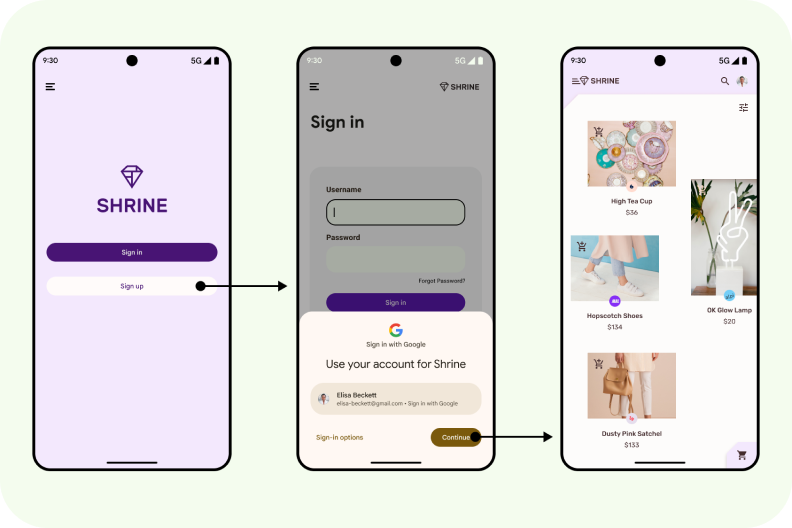
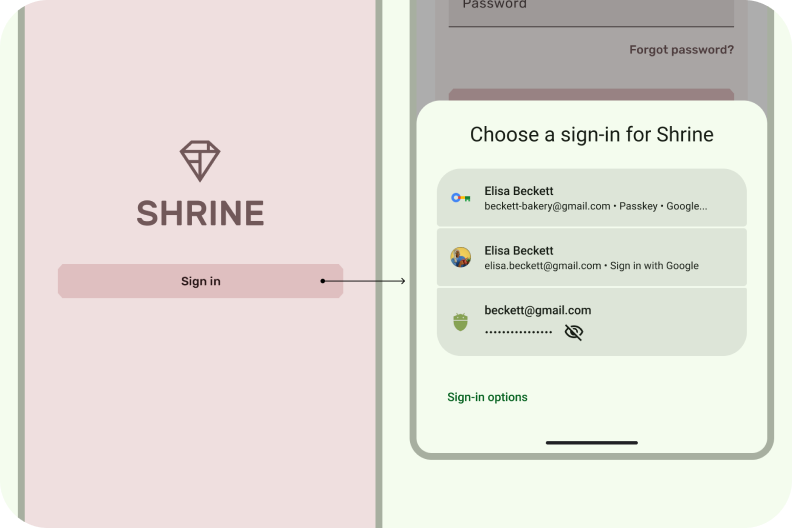
Um hub central para vários métodos de login, incluindo chaves de acesso. O Gerenciador de credenciais ajuda os usuários a fazer login no seu app com um único toque. Isso elimina a necessidade de os usuários lembrarem qual método eles precisam usar e se concentram em escolher a conta certa.
Login com um toque
Criação de conta simples
Interface unificada
Integrado ao Gerenciador de senhas do Google
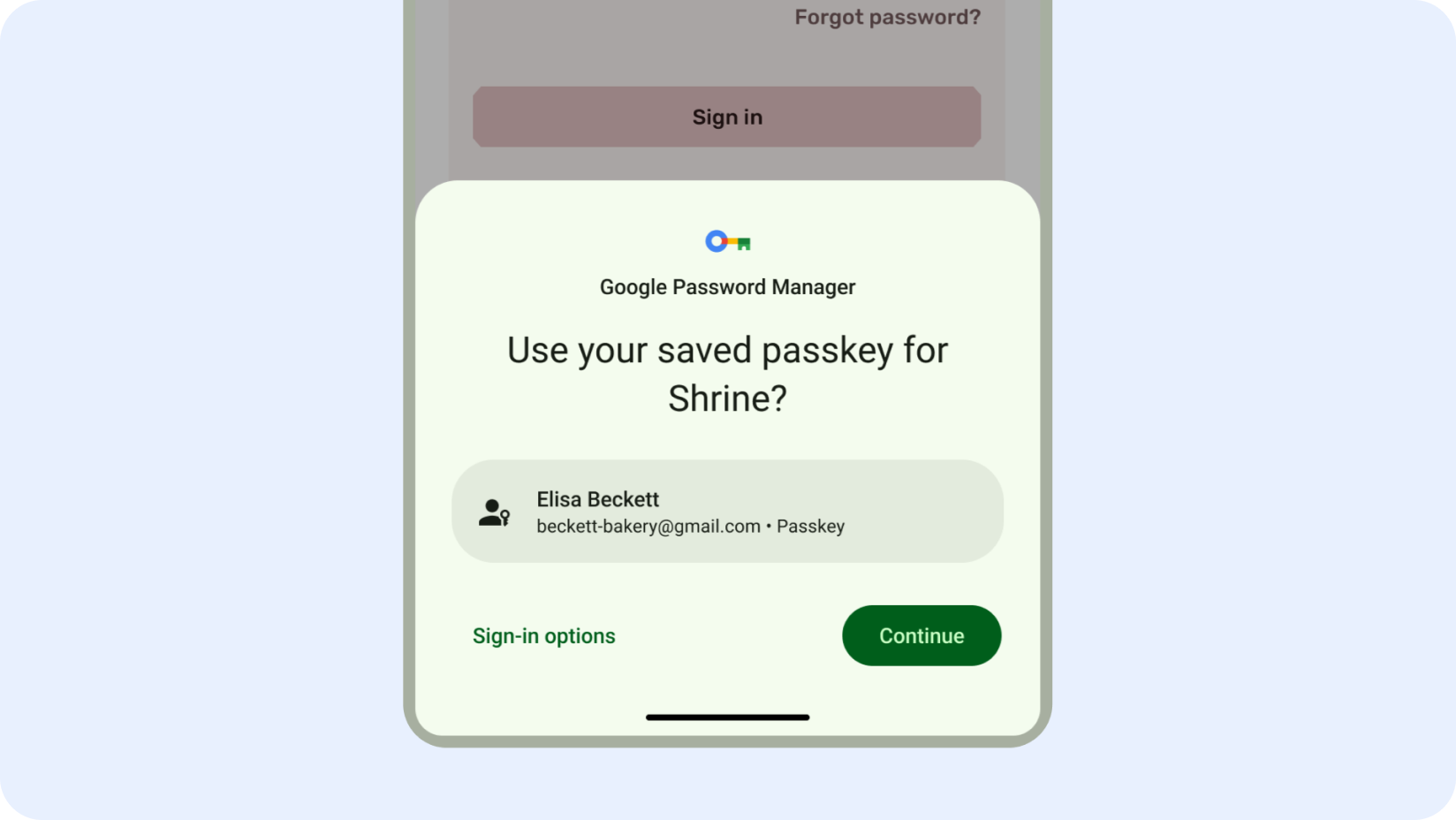
As chaves de acesso melhoram a experiência do usuário na autenticação no Android
O login pode ser uma grande fonte de confusão e abandono de apps.
As chaves de acesso, disponíveis no Gerenciador de credenciais, melhoram a experiência do usuário, facilitando e tornando o login mais seguro. Elas são resistentes a phishing e não podem ser reutilizadas. Os usuários podem fazer login desbloqueando o dispositivo com a impressão digital, o reconhecimento facial ou um PIN local, em vez de precisar lembrar e digitar uma senha.
Criação rápida de contas
Simplifique o processo de inscrição e reduza as taxas de abandono integrando o recurso "Fazer login com o Google" durante a criação da conta.
Essa opção de inscrição com um clique usa credenciais conhecidas do usuário, minimizando a fricção e melhorando a experiência do usuário.
Ao priorizar o recurso "Fazer login com o Google" na inscrição, você pode melhorar significativamente o processo de integração do app e a satisfação do usuário.
Login com um clique
O Gerenciador de credenciais é uma API do Jetpack que oferece suporte a vários métodos de login, como nome de usuário e senha, chaves de acesso e login federado (como o recurso Fazer login com o Google) em uma única API, simplificando a integração para desenvolvedores.
Os usuários podem fazer login no seu app com um único clique, sem se preocupar com a opção certa para escolher. O Gerenciador de credenciais unifica a interface de login em todos os métodos de autenticação, deixando o processo de login em apps mais claro e fácil, independente do método escolhido.
Começar a usar a autenticação
Autenticação do usuário com chaves de acesso
Integrar o Gerenciador de credenciais às chaves de acesso
Integrar o Gerenciador de credenciais ao recurso "Fazer login com o Google"
Integrar o Gerenciador de credenciais ao WebView
Integrar o Firebase Authentication ao recurso Fazer login com o Google
Notícias e vídeos mais recentes
Migrar de APIs legadas para o Gerenciador de credenciais
Migrar do Login do Google legado
O recurso "Fazer login com o Google" para Android foi descontinuado e será removido em 2025. Mude para o Gerenciador de credenciais para uma experiência do usuário mais tranquila e para manter seu app atualizado.
O Gerenciador de credenciais se concentra na inscrição e no login. Para autorização, use AuthorizationClient para solicitações de autorização granulares em Contas do Google (como o Drive, a Agenda ou o Fotos).