แพลตฟอร์ม Android 11 มีการเปลี่ยนแปลงลักษณะการทำงานที่อาจส่งผลต่อแอปของคุณ การเปลี่ยนแปลงลักษณะการทำงานต่อไปนี้จะมีผลกับ แอปทั้งหมด เมื่อแอปทำงานบน Android 11 ไม่ว่า targetSdkVersion จะเป็นเวอร์ชันใดก็ตาม คุณควรทดสอบแอปแล้วแก้ไขตามความจำเป็นเพื่อให้รองรับการเปลี่ยนแปลงเหล่านี้ได้อย่างเหมาะสม
โปรดตรวจสอบรายการการเปลี่ยนแปลงลักษณะการทำงานที่มีผลกับ แอปที่กำหนดเป้าหมายเป็น Android 11 เท่านั้นด้วย
ความเป็นส่วนตัว
Android 11 มีการเปลี่ยนแปลงและข้อจำกัดเพื่อเพิ่มความเป็นส่วนตัวของผู้ใช้ ซึ่งรวมถึงสิ่งต่อไปนี้
- สิทธิ์ครั้งเดียว: ให้ตัวเลือกแก่ผู้ใช้ ในการให้สิทธิ์เข้าถึงตำแหน่ง ไมโครโฟน และกล้องแบบชั่วคราวเพิ่มเติม
- การแสดงกล่องโต้ตอบสิทธิ์ การแสดงผล: การปฏิเสธสิทธิ์ซ้ำๆ ของสิทธิ์หมายความว่า "ไม่ต้องถามอีก"
- การตรวจสอบการเข้าถึงข้อมูล: รับ ข้อมูลเชิงลึกเกี่ยวกับตำแหน่งที่แอปเข้าถึงข้อมูลส่วนตัว ทั้งในโค้ดของแอปเอง และในโค้ดของไลบรารีที่แอปใช้
- สิทธิ์หน้าต่างการแจ้งเตือนของระบบ: ระบบจะให้สิทธิ์
SYSTEM_ALERT_WINDOWแก่แอปบางประเภทโดยอัตโนมัติเมื่อมีการขอ นอกจากนี้ Intent ที่มีการดำเนินการผ่าน IntentACTION_MANAGE_OVERLAY_PERMISSIONจะนำผู้ใช้ไปยังหน้าจอในการตั้งค่าระบบเสมอ - ตัวระบุ SIM ถาวร:
ใน Android 11 ขึ้นไป ระบบจะจำกัดการเข้าถึง ICCID ที่รีเซ็ตไม่ได้ผ่านเมธอด
getIccId()เมธอดจะแสดงผลสตริงว่างที่ไม่ใช่ Null หากต้องการระบุ SIM ที่ติดตั้งในอุปกรณ์อย่างไม่ซ้ำกัน ให้ใช้getSubscriptionId()เมธอดแทน รหัสการสมัครใช้บริการจะแสดงค่าดัชนี (เริ่มต้นที่ 1) เพื่อระบุ SIM ที่ติดตั้งอย่างไม่ซ้ำกัน ซึ่งรวมถึง SIM จริงและ SIM อิเล็กทรอนิกส์ ค่าของตัวระบุนี้จะคงที่สำหรับ SIM ที่กำหนด เว้นแต่จะมีการรีเซ็ตเป็นค่าเริ่มต้นจากโรงงาน
ดูข้อมูลเพิ่มเติมได้ที่หน้าความเป็นส่วนตัว
การแจ้งเตือนความเสี่ยงต่อการติดเชื้อ
Android 11 อัปเดตแพลตฟอร์มโดยคำนึงถึง ระบบการแจ้งเตือนความเสี่ยงต่อการติดเชื้อ ตอนนี้ผู้ใช้สามารถเรียกใช้แอปการแจ้งเตือนความเสี่ยงต่อการติดเชื้อใน Android 11 ได้โดยไม่ต้องเปิดการตั้งค่าตำแหน่งของอุปกรณ์ นี่เป็นข้อยกเว้นสำหรับระบบการแจ้งเตือนความเสี่ยงต่อการติดเชื้อเท่านั้น เนื่องจากระบบได้รับการออกแบบมาในลักษณะที่แอปที่ใช้ระบบนี้จะไม่สามารถอนุมานตำแหน่งของอุปกรณ์ผ่านการสแกนหาบลูทูธได้
เพื่อปกป้องความเป็นส่วนตัวของผู้ใช้ ระบบยังคงห้ามแอปอื่นๆ ทั้งหมดไม่ให้ทำการสแกนหาบลูทูธ เว้นแต่จะมีการเปิดการตั้งค่าตำแหน่งของอุปกรณ์และผู้ใช้ได้ให้สิทธิ์เข้าถึงตำแหน่งแก่แอป อ่านข้อมูลเพิ่มเติมได้ในโพสต์ การอัปเดตเกี่ยวกับการแจ้งเตือนความเสี่ยงต่อการติดเชื้อ
ความปลอดภัย
ซ็อกเก็ต SSL ใช้เอ็นจิน SSL ของ Conscrypt โดยค่าเริ่มต้น
การใช้งาน SSLSocket เริ่มต้นของ Android อิงตาม Conscrypt
ตั้งแต่ Android 11 เป็นต้นมา การใช้งานดังกล่าวสร้างขึ้นภายในโดยอิงตาม SSLEngine ของ Conscrypt
Scudo Hardened Allocator
Android 11 ใช้
Scudo Hardened Allocator
ภายในเพื่อให้บริการการจัดสรรฮีป Scudo สามารถตรวจจับและลดการละเมิดความปลอดภัยของหน่วยความจำบางประเภทได้ หากคุณเห็นข้อขัดข้องที่เกี่ยวข้องกับ Scudo
(เช่น Scudo ERROR:) ในรายงานข้อขัดข้องแบบเนทีฟ โปรดดู
เอกสารประกอบการแก้ปัญหา Scudo
สถิติการใช้งานแอป
Android 11 จะจัดเก็บสถิติการใช้งานแอปของผู้ใช้แต่ละรายไว้ในพื้นที่เก็บข้อมูลที่เข้ารหัสด้วยข้อมูลเข้าสู่ระบบเพื่อปกป้องผู้ใช้ได้ดียิ่งขึ้น ดังนั้น
ทั้งระบบและแอปใดๆ จะเข้าถึงข้อมูลดังกล่าวไม่ได้ เว้นแต่
isUserUnlocked()
จะแสดงผล true ซึ่งจะเกิดขึ้นหลังจากดำเนินการอย่างใดอย่างหนึ่งต่อไปนี้
- ผู้ใช้ปลดล็อกอุปกรณ์เป็นครั้งแรกหลังจากระบบเริ่มต้น
- ผู้ใช้เปลี่ยนไปใช้บัญชีของตนในอุปกรณ์
หากแอปของคุณผูกกับอินสแตนซ์ของ
UsageStatsManager อยู่แล้ว ให้ตรวจสอบ
ว่าคุณเรียกใช้เมธอดในออบเจ็กต์นี้หลังจากที่ผู้ใช้ปลดล็อกอุปกรณ์แล้ว
มิเช่นนั้น API จะแสดงผลค่า Null หรือค่าว่าง
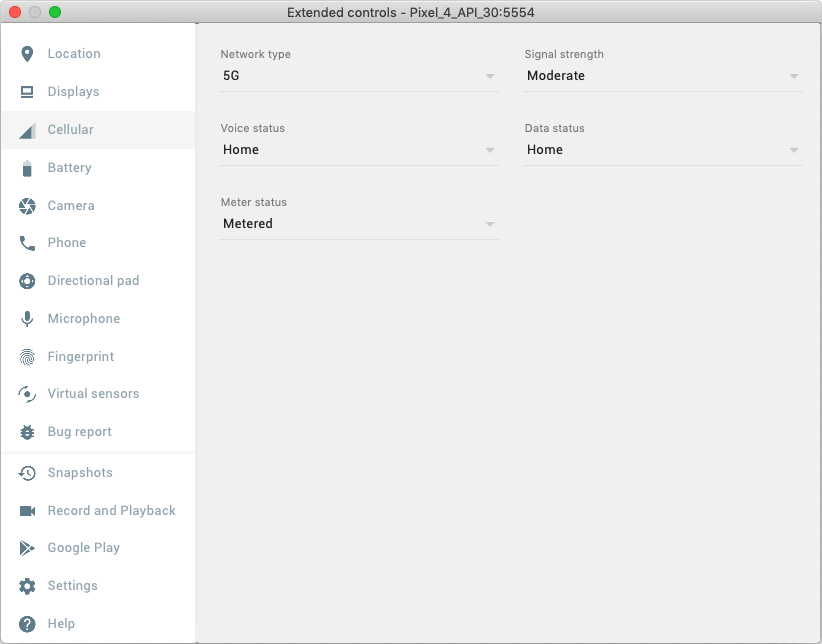
การรองรับอีมูเลเตอร์สำหรับ 5G
Android 11 เพิ่ม API 5G เพื่อให้
แอปของคุณเพิ่มฟีเจอร์ที่ล้ำสมัยได้ หากต้องการทดสอบฟีเจอร์ขณะเพิ่ม
คุณสามารถใช้ความสามารถใหม่ของอีมูเลเตอร์
Android SDKได้ ฟังก์ชันการทำงานใหม่นี้ได้รับการเพิ่มในอีมูเลเตอร์เวอร์ชัน 30.0.22 การเลือกการตั้งค่าเครือข่าย 5G
จะตั้งค่า
TelephonyDisplayInfo เป็น
OVERRIDE_NETWORK_TYPE_NR_NSA แก้ไขแบนด์วิดท์โดยประมาณ และช่วยให้คุณตั้งค่าการใช้งานแบบคิดตามปริมาณข้อมูลเพื่อยืนยัน
ว่าแอปตอบสนองต่อการเปลี่ยนแปลงสถานะ
NET_CAPABILITY_TEMPORARILY_NOT_METERED
ได้อย่างเหมาะสม
ประสิทธิภาพและการแก้ไขข้อบกพร่อง
การแก้ไขข้อบกพร่องของการจำกัดการเรียก API ของ JobScheduler
Android 11 มีการรองรับการแก้ไขข้อบกพร่องเพื่อให้แอประบุการเรียก API ของ JobScheduler ที่อาจเกินขีดจำกัดอัตราที่กำหนด
นักพัฒนาแอปสามารถใช้ฟีเจอร์นี้เพื่อระบุปัญหาด้านประสิทธิภาพที่อาจเกิดขึ้น สำหรับ
แอปที่มีแอตทริบิวต์ debuggable ของไฟล์ Manifest ตั้งค่าเป็น "จริง" การเรียก API
ของ JobScheduler ที่เกินขีดจำกัดอัตราจะแสดงผล RESULT_FAILURE
ระบบจะกำหนดขีดจำกัดในลักษณะที่ Use Case ที่ถูกต้องจะไม่ได้รับผลกระทบ
ตัวล้างตัวบอกไฟล์ (fdsan)
Android 10 เปิดตัว fdsan (ตัวล้างตัวบอกไฟล์)
fdsan จะตรวจจับการจัดการความเป็นเจ้าของตัวบอกไฟล์ที่ไม่ถูกต้อง เช่น การใช้หลังจากปิดและการปิดซ้ำ โหมดเริ่มต้นของ fdsan จะมีการเปลี่ยนแปลงใน Android 11 ตอนนี้ fdsan จะยกเลิกเมื่อตรวจพบข้อผิดพลาด ซึ่งลักษณะการทำงานก่อนหน้านี้คือการบันทึกคำเตือนและดำเนินการต่อ หากคุณเห็นข้อขัดข้อง
เนื่องจาก fdsan ในแอปพลิเคชัน โปรดดู
fdsan documentation
ข้อจำกัดเกี่ยวกับอินเทอร์เฟซที่ไม่ใช่ SDK
Android 11 มีรายการอินเทอร์เฟซที่ไม่ใช่ SDK ที่ถูกจำกัดซึ่งอัปเดตแล้ว โดยอิงตามการทำงานร่วมกับนักพัฒนาแอป Android และการทดสอบภายในล่าสุด เราจะตรวจสอบว่ามีทางเลือกอื่นที่เผยแพร่ต่อสาธารณะพร้อมใช้งานก่อนที่จะจำกัดอินเทอร์เฟซที่ไม่ใช่ SDK ทุกครั้งที่ทำได้
หากแอปของคุณไม่ได้กำหนดเป้าหมายเป็น Android 11 การเปลี่ยนแปลงบางอย่างเหล่านี้อาจไม่ส่งผลกระทบต่อคุณในทันที อย่างไรก็ตาม แม้ว่าปัจจุบันคุณจะใช้ อินเทอร์เฟซที่ไม่ใช่ SDK บางรายการได้ (ขึ้นอยู่กับระดับ API เป้าหมายของแอป) แต่การใช้เมธอดหรือฟิลด์ที่ไม่ใช่ SDK ใดๆ ก็มีความเสี่ยงสูงที่จะทำให้แอป ขัดข้องเสมอ
หากต้องการดูว่าแอปใช้อินเทอร์เฟซที่ไม่ใช่ SDK อยู่หรือเปล่า คุณสามารถทดสอบแอปดูได้ หากแอปของคุณใช้อินเทอร์เฟซที่ไม่ใช่ SDK คุณควรเริ่มวางแผนย้ายไปใช้ทางเลือกอื่นที่เป็น SDK อย่างไรก็ตาม เราเข้าใจว่าแอปบางแอปมี Use Case ที่ถูกต้องสำหรับการใช้อินเทอร์เฟซที่ไม่ใช่ SDK หากไม่พบวิธีอื่นแทนการใช้อินเทอร์เฟซที่ไม่ใช่ SDK สำหรับฟีเจอร์ในแอป คุณควรขอ API สาธารณะใหม่
ดูข้อมูลเพิ่มเติมเกี่ยวกับการเปลี่ยนแปลงใน Android เวอร์ชันนี้ได้ที่การอัปเดต ข้อจำกัดเกี่ยวกับอินเทอร์เฟซที่ไม่ใช่ SDK ใน Android 11 ดูข้อมูลเพิ่มเติมเกี่ยวกับอินเทอร์เฟซที่ไม่ใช่ SDK โดยทั่วไปได้ที่ ข้อจำกัดเกี่ยวกับอินเทอร์เฟซที่ไม่ใช่ SDK อินเทอร์เฟซ
นำไลบรารีที่ใช้ร่วมกันของ Maps v1 ออกแล้ว
ระบบได้นำไลบรารีที่ใช้ร่วมกันของ Maps เวอร์ชัน 1 ออกจาก Android 11 อย่างสมบูรณ์แล้ว ก่อนหน้านี้ไลบรารีนี้เลิกใช้งานแล้วและหยุดทำงานสำหรับแอปใน Android 10 แอปที่เคยใช้ ไลบรารีที่ใช้ร่วมกันนี้สำหรับอุปกรณ์ที่ใช้ Android 9 (API ระดับ 28) หรือต่ำกว่า ควรใช้ Maps SDK สำหรับ Android แทน
การโต้ตอบกับแอปอื่นๆ
แชร์ URI เนื้อหา
หากแอปของคุณแชร์ URI เนื้อหากับแอปอื่น Intent ต้องให้สิทธิ์เข้าถึง URI
โดยตั้งค่าแฟล็ก Intent อย่างน้อย 1 รายการต่อไปนี้:
FLAG_GRANT_READ_URI_PERMISSION
และ
FLAG_GRANT_WRITE_URI_PERMISSION
วิธีนี้จะช่วยให้แอปอื่นยังเข้าถึง URI เนื้อหาได้แม้ว่าแอปนั้นจะกำหนดเป้าหมายเป็น Android 11 แอปของคุณต้องมีแฟล็ก Intent แม้ว่า URI เนื้อหาจะเชื่อมโยงกับผู้ให้บริการเนื้อหาที่แอปของคุณไม่ได้เป็นเจ้าของก็ตาม
หากแอปของคุณเป็นเจ้าของผู้ให้บริการเนื้อหาที่เชื่อมโยงกับ URI เนื้อหา ให้ตรวจสอบว่าไม่ได้ส่งออกผู้ให้บริการเนื้อหา เราแนะนำแนวทางปฏิบัติแนะนำด้านความปลอดภัยนี้อยู่แล้ว
การโหลดไลบรารี
การโหลดไลบรารีทั่วไปของ ICU ด้วยเส้นทางแบบสัมบูรณ์
แอปที่กำหนดเป้าหมายเป็น API ระดับ 28 และต่ำกว่าจะไม่สามารถใช้ dlopen(3) เพื่อโหลด libicuuc ด้วยเส้นทางแบบสัมบูรณ์ "/system/lib/libicuuc.so" สำหรับแอปเหล่านั้น
dlopen("/system/lib/libicuuc.so", ...) จะแสดงผลแฮนเดิล Null
ให้ใช้ชื่อไลบรารีเป็นชื่อไฟล์เพื่อโหลดไลบรารี เช่น
dlopen("libicuuc.so", ...)

