El programa de mejora de la seguridad de las apps es un servicio que se brinda a los desarrolladores de apps para Google Play con el objetivo de mejorar la seguridad de sus apps. El programa proporciona sugerencias y recomendaciones para crear apps más seguras e identifica posibles mejoras de seguridad cuando tus apps se suben a Google Play. Hasta la fecha, el programa permitió que los desarrolladores corrijan más de 1,000,000 de apps en Google Play.
Cómo funciona
Antes de que se acepten las apps en Google Play, las analizamos en busca de posibles problemas de seguridad. También volvemos a analizar de manera continua más de un millón de apps en Google Play para detectar amenazas adicionales.
Si tu app está marcada por un posible problema de seguridad, te lo notificaremos de inmediato para ayudarte a resolver el problema rápidamente y a mantener la seguridad de tus usuarios. Te enviaremos alertas a través de correo electrónico y Google Play Console con vínculos a una página de asistencia donde se detalla cómo puedes mejorar la aplicación.
Por lo general, estas notificaciones incluirán un cronograma para entregar la mejora a los usuarios lo más rápido posible. Para algunos tipos de problemas, quizá te solicitemos que realices mejoras de seguridad en la app antes de poder publicar más actualizaciones.
Puedes confirmar que resolviste por completo el problema subiendo la nueva versión de tu app a Google Play Console. Asegúrate de cambiar el número de versión de la app corregida por un número superior. Después de unas horas, revisa Play Console para ver la alerta de seguridad. Si no la ves, significa que ya está todo listo.
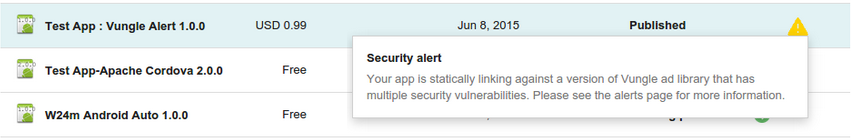
Ejemplo de una alerta de mejora de seguridad para una app en Play Console.
Participa
El éxito de este programa depende de nuestra asociación con los desarrolladores de apps para Google Play y con la comunidad de seguridad. Todos somos responsables de proporcionarles apps seguras a nuestros usuarios. Si tienes comentarios o preguntas, comunícate con nosotros a través del Centro de ayuda de Google Play para desarrolladores. Para informar sobre posibles problemas de seguridad en las apps, comunícate con nosotros a través de security+asi@android.com.
Campañas y soluciones
A continuación, se muestran los problemas de seguridad más recientes que se informaron a los desarrolladores en Google Play. Puedes encontrar más detalles sobre la vulnerabilidad y las soluciones en el vínculo de la página de ayuda de cada campaña.
Tabla 1: Campañas de advertencia con fecha límite asociada para la solución.
| Campaña | Iniciado | Página de asistencia |
|---|---|---|
| Claves expuestas del servidor de Firebase Cloud Messaging | 12/10/2021 | Página de asistencia |
| Redireccionamiento de intents | 16/5/2019 | Página de asistencia |
| Inyección de la interfaz de JavaScript | 4/12/2018 | Página de asistencia |
| Usurpación de esquemas | 15/11/2018 | Página de asistencia |
| Ejecución de secuencias de comandos entre apps | 30/10/2018 | Página de asistencia |
| Ejecución de secuencias de comandos entre sitios basadas en archivos | 5/6/2018 | Página de asistencia |
| Inyección de SQL | 4/6/2018 | Página de asistencia |
| Salto de directorio | 22/9/2017 | Página de asistencia |
| Verificación de nombre de host no seguro | 29/11/2016 | Página de asistencia |
| Inyección de fragmento | 29/11/2016 | Página de asistencia |
| SDK de anuncios supersónicos | 28/9/2016 | Página de asistencia |
| Libpng | 16/6/2016 | Página de asistencia |
| Libjpeg-turbo | 16/6/2016 | Página de asistencia |
| SDK de anuncios de Vpon | 16/6/2016 | Página de asistencia |
| SDK de anuncios de Airpush | 31/3/2016 | Página de asistencia |
| SDK de anuncios de MoPub | 31/3/2016 | Página de asistencia |
| OpenSSL ("logjam" y CVE-2015-3194, CVE-2014-0224) | 31/3/2016 | Página de asistencia |
| TrustManager | 17/2/2016 | Página de asistencia |
| AdMarvel | 8/2/2016 | Página de asistencia |
| Libupup (CVE-2015-8540) | 8/2/2016 | Página de asistencia |
| Apache Cordova (CVE-2015-5256, CVE-2015-1835) | 14/12/2015 | Página de asistencia |
| SDK de anuncios de Vitamio | 14/12/2015 | Página de asistencia |
| GnuTLS | 13/10/2015 | Página de asistencia |
| Webview SSLErrorHandler | 17/7/2015 | Página de asistencia |
| SDK de anuncios de Vungle | 29/6/2015 | Página de asistencia |
| Apache Cordova (CVE-2014-3500, CVE-2014-3501, CVE-2014-3502) | 29/6/2015 | Página de asistencia |
Tabla 2: Campañas de solo advertencia (sin fecha límite para la solución)
| Campaña | Iniciado | Página de asistencia |
|---|---|---|
| PendingIntent implícito | 22/2/2022 | Página de asistencia |
| Intent interno implícito | 22/6/2021 | Página de asistencia |
| Modo de encriptación no seguro | 13/10/2020 | Página de asistencia |
| Encriptación no segura | 17/9/2019 | Página de asistencia |
| Salto de directorio de ZipFile | 21/5/2019 | Página de asistencia |
| Token OAuth de Foursquare incorporado | 28/9/2016 | Página de asistencia |
| Token OAuth de Facebook incorporado | 28/9/2016 | Página de asistencia |
| Interceptación de Facturación Google Play | 28/7/2016 | Página de asistencia |
| Token de actualización OAuth de Google incorporado | 28/7/2016 | Página de asistencia |
| Credenciales filtradas de la URL del desarrollador | 16/6/2016 | Página de asistencia |
| Archivos de almacén de claves incorporados | 2/10/2014 | |
| Credenciales incorporadas de Amazon Web Services | 12/6/2014 |
