A plataforma Android 16 inclui mudanças de comportamento que podem afetar seu app.
As mudanças de comportamento a seguir se aplicam a todos os apps quando executados no Android 16,
independente de targetSdkVersion. Teste seu app e modifique-o conforme necessário para ficar compatível com essas mudanças, se necessário.
Consulte também a lista de mudanças de comportamento que afetam apenas os apps destinados ao Android 16.
Funcionalidade principal
O Android 16 (nível 36 da API) inclui as seguintes mudanças que modificam ou expandem vários recursos principais do sistema Android.
Otimizações de cota do JobScheduler
Starting in Android 16, we're adjusting regular and expedited job execution runtime quota based on the following factors:
- Which app standby bucket the application is in: in Android 16, active standby buckets will start being enforced by a generous runtime quota.
- If the job starts execution while the app is in a top state: in Android 16, Jobs started while the app is visible to the user and continues after the app becomes invisible, will adhere to the job runtime quota.
- If the job is executing while running a Foreground Service: in Android 16, jobs that are executing concurrently with a foreground service will adhere to the job runtime quota. If you're leveraging jobs for user initiated data transfer, consider using user initiated data transfer jobs instead.
This change impacts tasks scheduled using WorkManager, JobScheduler, and
DownloadManager. To debug why a job was stopped, we recommend logging why your
job was stopped by calling WorkInfo.getStopReason() (for
JobScheduler jobs, call JobParameters.getStopReason()).
For information about how your app's state affects the resources it can use, see Power management resource limits. For more information on battery-optimal best practices, refer to guidance on optimize battery use for task scheduling APIs.
We also recommend leveraging the new
JobScheduler#getPendingJobReasonsHistory API introduced in
Android 16 to understand why a job has not executed.
Testing
To test your app's behavior, you can enable override of certain job quota optimizations as long as the app is running on an Android 16 device.
To disable enforcement of "top state will adhere to job runtime quota", run the
following adb command:
adb shell am compat enable OVERRIDE_QUOTA_ENFORCEMENT_TO_TOP_STARTED_JOBS APP_PACKAGE_NAME
To disable enforcement of "jobs that are executing while concurrently with a
foreground service will adhere to the job runtime quota", run the following
adb command:
adb shell am compat enable OVERRIDE_QUOTA_ENFORCEMENT_TO_FGS_JOBS APP_PACKAGE_NAME
To test certain app standby bucket behavior, you can set the app standby bucket
of your app using the following adb command:
adb shell am set-standby-bucket APP_PACKAGE_NAME active|working_set|frequent|rare|restricted
To understand the app standby bucket your app is in, you can get the app standby
bucket of your app using the following adb command:
adb shell am get-standby-bucket APP_PACKAGE_NAME
Motivo de interrupção de jobs vazios abandonados
An abandoned job occurs when the JobParameters object associated with the job
has been garbage collected, but JobService#jobFinished(JobParameters,
boolean) has not been called to signal job completion. This indicates that
the job may be running and being rescheduled without the app's awareness.
Apps that rely on JobScheduler, don't maintain a strong reference to the
JobParameters object, and timeout will now be granted the new job stop reason
STOP_REASON_TIMEOUT_ABANDONED, instead of STOP_REASON_TIMEOUT.
If there are frequent occurrences of the new abandoned stop reason, the system will take mitigation steps to reduce job frequency.
Apps should use the new stop reason to detect and reduce abandoned jobs.
If you're using WorkManager, AsyncTask, or DownloadManager, you aren't impacted because these APIs manage the job lifecycle on your app's behalf.
Suspensão total de JobInfo#setImportantWhileForeground
O método JobInfo.Builder#setImportantWhileForeground(boolean)
indica a importância de um job enquanto o app de programação está em primeiro plano
ou quando é temporariamente isento de restrições em segundo plano.
Esse método foi descontinuado a partir do Android 12 (nível 31 da API). A partir do Android 16, ele não funciona mais de forma eficaz, e a chamada desse método será ignorada.
Essa remoção de funcionalidade também se aplica a
JobInfo#isImportantWhileForeground(). A partir do Android
16, se o método for chamado, ele retornará false.
O escopo de prioridade de transmissão ordenada não é mais global
Os apps Android podem definir prioridades em broadcast receivers para controlar
a ordem em que os receptores recebem e processam a transmissão. Para
recebedores declarados no manifesto, os apps podem usar o atributo
android:priority para definir a prioridade. Para
recebedores registrados no contexto, os apps podem usar a
API IntentFilter#setPriority() para definir a prioridade. Quando
uma transmissão é enviada, o sistema a entrega aos receptores na ordem de
prioridade, da mais alta para a mais baixa.
No Android 16, a ordem de entrega de transmissão usando o atributo android:priority
ou IntentFilter#setPriority() em diferentes processos não será
garantida. As prioridades de transmissão só serão respeitadas no mesmo
processo do aplicativo, e não em todos os processos.
Além disso, as prioridades de transmissão serão automaticamente limitadas ao intervalo
(SYSTEM_LOW_PRIORITY + 1,
SYSTEM_HIGH_PRIORITY - 1). Somente os componentes do sistema poderão
definir SYSTEM_LOW_PRIORITY, SYSTEM_HIGH_PRIORITY como prioridade de
transmissão.
O app pode ser afetado se fizer o seguinte:
- Seu aplicativo declarou vários processos com a mesma intent de transmissão e tem expectativas em relação ao recebimento dessas intents em uma determinada ordem com base na prioridade.
- O processo do aplicativo interage com outros processos e tem expectativas em relação ao recebimento de uma intent de transmissão em uma determinada ordem.
Se os processos precisarem se coordenar, eles vão precisar se comunicar usando outros canais de coordenação.
Mudanças internas do ART
Android 16 includes the latest updates to the Android Runtime (ART) that improve the Android Runtime's (ART's) performance and provide support for additional Java features. Through Google Play System updates, these improvements are also available to over a billion devices running Android 12 (API level 31) and higher.
As these changes are released, libraries and app code that rely on internal structures of ART might not work correctly on devices running Android 16, along with earlier Android versions that update the ART module through Google Play system updates.
Relying on internal structures (such as non-SDK interfaces) can always lead to compatibility problems, but it's particularly important to avoid relying on code (or libraries containing code) that leverages internal ART structures, since ART changes aren't tied to the platform version the device is running on and they go out to over a billion devices through Google Play system updates.
All developers should check whether their app is impacted by testing their apps thoroughly on Android 16. In addition, check the known issues to see if your app depends on any libraries that we've identified that rely on internal ART structures. If you do have app code or library dependencies that are affected, seek public API alternatives whenever possible and request public APIs for new use cases by creating a feature request in our issue tracker.
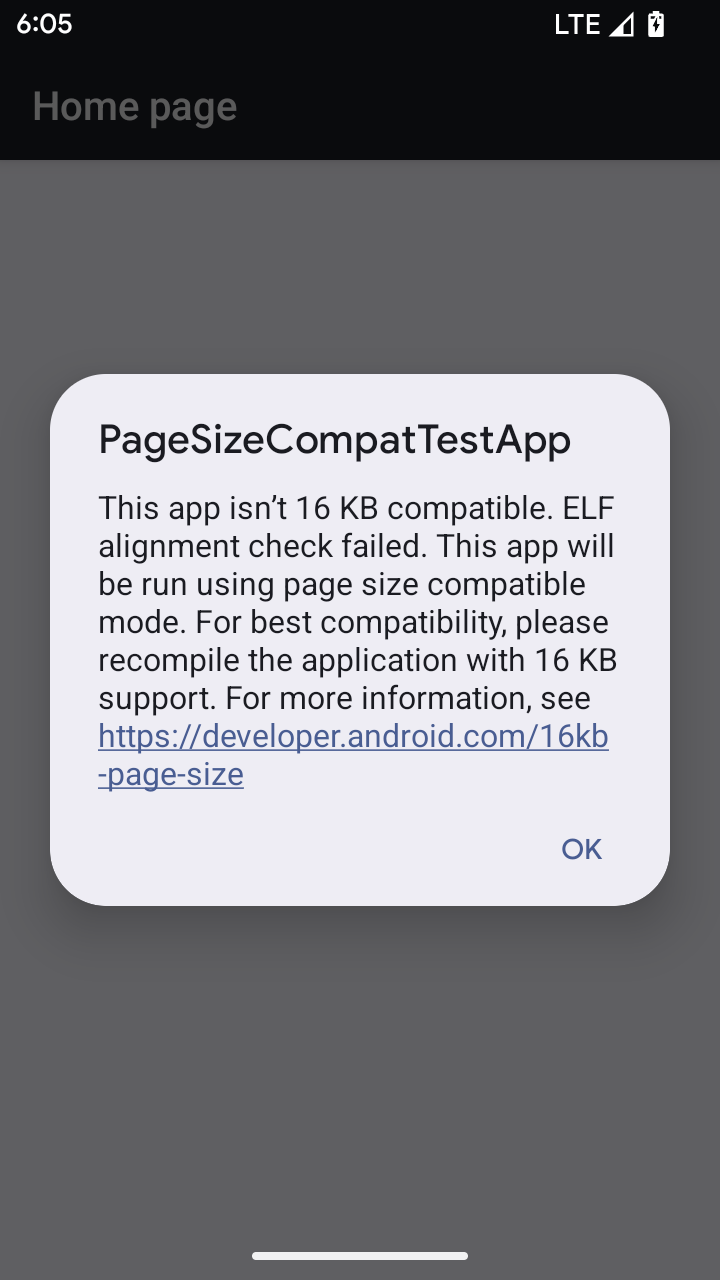
Modo de compatibilidade de tamanho de página de 16 KB
O Android 15 introduziu o suporte a páginas de memória de 16 KB para otimizar o desempenho da plataforma. O Android 16 adiciona um modo de compatibilidade, permitindo que alguns apps criados para páginas de memória de 4 KB sejam executados em um dispositivo configurado para páginas de memória de 16 KB.
Quando o app está em execução em um dispositivo com o Android 16 ou mais recente, se o Android
detectar que o app tem páginas de memória alinhadas de 4 KB, ele vai usar automaticamente
o modo de compatibilidade e mostrar uma caixa de diálogo de notificação para o usuário. Definir a
propriedade android:pageSizeCompat no AndroidManifest.xml para ativar o
modo de compatibilidade com versões anteriores vai impedir a exibição da caixa de diálogo quando o
app for iniciado. Para usar a propriedade android:pageSizeCompat, compile o app
usando o SDK do Android 16.
Para ter o melhor desempenho, confiabilidade e estabilidade, o app ainda precisa ter 16 KB alinhados. Confira nossa postagem recente do blog sobre como atualizar seus apps para oferecer suporte a páginas de memória de 16 KB para mais detalhes.
Experiência do usuário e interface do sistema
O Android 16 (nível 36 da API) inclui as seguintes mudanças que têm como objetivo criar uma experiência do usuário mais consistente e intuitiva.
Suspensão de anúncios de acessibilidade disruptivos
O Android 16 descontinua os avisos de acessibilidade, caracterizados pelo uso de
announceForAccessibility ou o envio de
eventos de acessibilidade TYPE_ANNOUNCEMENT. Isso pode criar
experiências de usuário inconsistentes para usuários do TalkBack e do leitor de tela do Android.
As alternativas atendem melhor a uma gama mais ampla de necessidades dos usuários em várias
tecnologias assistivas do Android.
Exemplos de alternativas:
- Para mudanças significativas na interface, como mudanças de janela, use
Activity.setTitle(CharSequence)esetAccessibilityPaneTitle(java.lang.CharSequence). No Compose, useModifier.semantics { paneTitle = "paneTitle" }. - Para informar o usuário sobre mudanças na interface crítica, use
setAccessibilityLiveRegion(int). No Compose, useModifier.semantics { liveRegion = LiveRegionMode.[Polite|Assertive]}. Elas devem ser usadas com moderação, porque podem gerar avisos sempre que uma visualização é atualizada. - Para notificar os usuários sobre erros, envie um
AccessibilityEventdo tipoAccessibilityEvent#CONTENT_CHANGE_TYPE_ERRORe definaAccessibilityNodeInfo#setError(CharSequence)ou useTextView#setError(CharSequence).
A documentação de referência da API announceForAccessibility, que foi descontinuada, inclui mais detalhes sobre as alternativas sugeridas.
Suporte à navegação com três botões
Android 16 brings predictive back support to the 3-button navigation for apps that have properly migrated to predictive back. Long-pressing the back button initiates a predictive back animation, giving you a preview of where the back swipe takes you.
This behavior applies across all areas of the system that support predictive back animations, including the system animations (back-to-home, cross-task, and cross-activity).
Ícones temáticos automáticos de apps
A partir do Android 16 QPR 2, o Android aplica temas automaticamente aos ícones de apps para criar uma experiência coesa na tela inicial. Isso acontece se um app não fornecer um ícone temático próprio. Os apps podem controlar o design do ícone temático incluindo uma camada monocromática no ícone adaptável e conferindo uma prévia da aparência do ícone no Android Studio.
Formatos de dispositivos
O Android 16 (nível 36 da API) inclui as seguintes mudanças para apps quando projetados em telas por proprietários de dispositivos virtuais.
Substituições do proprietário do dispositivo virtual
A virtual device owner is a trusted or privileged app that creates and manages a virtual device. Virtual device owners run apps on a virtual device and then project the apps to the display of a remote device, such as a personal computer, virtual reality device, or car infotainment system. The virtual device owner is on a local device, such as a mobile phone.
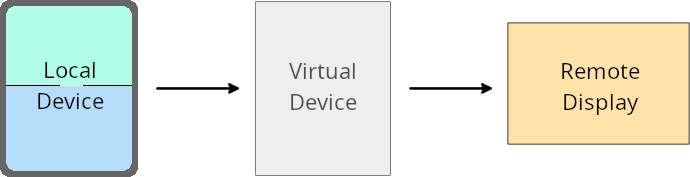
Per-app overrides
On devices running Android 16 (API level 36), virtual device owners can override app settings on select virtual devices that the virtual device owners manage. For example, to improve app layout, a virtual device owner can ignore orientation, aspect ratio, and resizability restrictions when projecting apps onto an external display.
Common breaking changes
The Android 16 behavior might impact your app's UI on large screen form factors such as car displays or Chromebooks, especially layouts that were designed for small displays in portrait orientation. To learn how to make your app adaptive for all device form factors, see About adaptive layouts.
References
Segurança
O Android 16 (nível 36 da API) inclui mudanças que promovem a segurança do sistema para ajudar a proteger apps e usuários contra apps maliciosos.
Segurança aprimorada contra ataques de redirecionamento de intents
O Android 16 oferece segurança padrão contra ataques gerais de redirecionamento de Intent, com compatibilidade mínima e mudanças necessárias para desenvolvedores.
Estamos introduzindo soluções de reforço da proteção de segurança padrão para exploits de redirecionamento de Intent. Na maioria dos casos, os apps que usam intents normalmente não apresentam problemas de compatibilidade. Coletamos métricas durante todo o processo de desenvolvimento para monitorar quais apps podem apresentar falhas.
O redirecionamento de intents no Android ocorre quando um invasor pode controlar total ou parcialmente o conteúdo de uma intent usada para iniciar um novo componente no contexto de um app vulnerável, enquanto o app da vítima inicia uma intent de subnível não confiável em um campo de extras de uma intent ("de nível superior"). Isso pode levar o app invasor a iniciar componentes particulares no contexto do app da vítima, acionando ações privilegiadas ou ganhando acesso de URI a dados sensíveis, o que pode levar ao roubo de dados e à execução de código arbitrário.
Desativar o processamento de redirecionamento de intents
O Android 16 apresenta uma nova API que permite que os apps desativem as proteções de segurança de inicialização. Isso pode ser necessário em casos específicos em que o comportamento de segurança padrão interfere em casos de uso legítimos do app.
Para aplicativos compilados com o SDK do Android 16 (nível 36 da API) ou mais recente
Você pode usar diretamente o método removeLaunchSecurityProtection() no objeto Intent.
val i = intent
val iSublevel: Intent? = i.getParcelableExtra("sub_intent")
iSublevel?.removeLaunchSecurityProtection() // Opt out from hardening
iSublevel?.let { startActivity(it) }
Para aplicativos compilados com o Android 15 (nível 35 da API) ou versões anteriores
Embora não seja recomendado, você pode usar a reflexão para acessar o método removeLaunchSecurityProtection().
val i = intent
val iSublevel: Intent? = i.getParcelableExtra("sub_intent", Intent::class.java)
try {
val removeLaunchSecurityProtection = Intent::class.java.getDeclaredMethod("removeLaunchSecurityProtection")
removeLaunchSecurityProtection.invoke(iSublevel)
} catch (e: Exception) {
// Handle the exception, e.g., log it
} // Opt-out from the security hardening using reflection
iSublevel?.let { startActivity(it) }
Apps complementares não são mais notificados sobre tempos limite de descoberta
Android 16 introduces a new behavior during
companion device pairing flow to protect the user's location
privacy from malicious apps. All companion apps running on Android 16 are no
longer directly notified of discovery timeout using
RESULT_DISCOVERY_TIMEOUT. Instead, the user is
notified of timeout events with a visual dialog. When the user dismisses
the dialog, the app is alerted of the association failure with
RESULT_USER_REJECTED.
The search duration has also been extended from the original 20 seconds, and the device discovery can be stopped by the user at any point during the search. If at least one device was discovered within the first 20 seconds of starting the search, the CDM stops searching for additional devices.
Conectividade
O Android 16 (nível 36 da API) inclui as seguintes mudanças na pilha do Bluetooth para melhorar a conectividade com dispositivos periféricos.
Melhoria no tratamento de perda de vínculo
A partir do Android 16, a pilha Bluetooth foi atualizada para melhorar a segurança e a experiência do usuário quando uma perda de vínculo remoto é detectada. Antes, o sistema retirava automaticamente a vinculação e iniciava um novo processo de pareamento, o que poderia levar a um novo pareamento não intencional. Em muitos casos, os apps não tratavam o evento de perda de vínculo de forma consistente.
Para unificar a experiência, o Android 16 melhorou o processamento de perda de vínculo para o sistema. Se um dispositivo Bluetooth pareado anteriormente não puder ser autenticado na reconexão, o sistema desconectará o link, manterá as informações de pareamento local e exibirá uma caixa de diálogo do sistema informando os usuários sobre a perda de pareamento e orientando-os a fazer o pareamento novamente.

