Platform Android 15 menyertakan perubahan perilaku yang mungkin memengaruhi aplikasi Anda.
Perubahan perilaku berikut ini berlaku untuk semua aplikasi saat dijalankan di Android 15,
terlepas dari targetSdkVersion. Sebaiknya uji aplikasi Anda, lalu modifikasi sesuai kebutuhan untuk mendukung perubahan ini dengan tepat, jika memungkinkan.
Selain itu, pastikan Anda meninjau daftar perubahan perilaku yang hanya memengaruhi aplikasi yang menargetkan Android 15.
Fungsi inti
Android 15 mengubah atau memperluas berbagai kemampuan inti sistem Android.
Perubahan pada status paket dihentikan
Tujuan status FLAG_STOPPED paket (yang dapat digunakan pengguna
dalam build AOSP dengan menekan lama ikon aplikasi dan memilih "Paksa
Berhenti") selalu untuk mempertahankan aplikasi dalam status ini hingga pengguna secara eksplisit
menghapus aplikasi dari status ini dengan langsung meluncurkan aplikasi atau secara tidak langsung
berinteraksi dengan aplikasi (melalui sharesheet atau widget, memilih aplikasi
sebagai wallpaper hidup, dll.). Di Android 15, kami telah memperbarui perilaku
sistem agar selaras dengan perilaku yang diinginkan ini. Aplikasi hanya boleh dihapus
dari status dihentikan melalui tindakan pengguna langsung atau tidak langsung.
Untuk mendukung perilaku yang diinginkan, selain batasan yang ada, sistem juga membatalkan semua intent yang tertunda saat aplikasi memasuki
status dihentikan di perangkat yang menjalankan Android 15. Saat tindakan pengguna menghapus
aplikasi dari status dihentikan, siaran ACTION_BOOT_COMPLETED
akan dikirim ke aplikasi yang memberikan peluang untuk mendaftarkan ulang
intent yang tertunda.
Anda dapat memanggil metode
ApplicationStartInfo.wasForceStopped()
baru untuk mengonfirmasi apakah aplikasi dimasukkan ke dalam status dihentikan.
Dukungan untuk ukuran halaman 16 KB
Sebelumnya, Android hanya mendukung ukuran halaman memori 4 KB, yang telah mengoptimalkan performa memori sistem untuk jumlah total memori rata-rata yang biasanya dimiliki perangkat Android. Mulai dari Android 15, AOSP mendukung perangkat yang dikonfigurasi untuk menggunakan ukuran halaman 16 KB (perangkat 16 KB). Jika aplikasi Anda menggunakan library NDK, baik secara langsung maupun tidak langsung melalui SDK, Anda harus membangun ulang aplikasi agar dapat berfungsi di perangkat 16 KB ini.
Seiring produsen perangkat terus membuat perangkat dengan jumlah memori fisik (RAM) yang lebih besar, banyak perangkat ini akan mengadopsi ukuran halaman 16 KB (dan pada akhirnya lebih besar) untuk mengoptimalkan performa perangkat. Menambahkan dukungan untuk perangkat dengan ukuran halaman 16 KB memungkinkan aplikasi Anda berjalan di perangkat ini dan membantu aplikasi Anda mendapatkan manfaat dari peningkatan performa terkait. Tanpa dikompilasi ulang, aplikasi tidak akan berfungsi di perangkat 16 KB dalam rilis Android mendatang.
Untuk membantu Anda menambahkan dukungan bagi aplikasi, kami telah memberikan panduan tentang cara memeriksa apakah aplikasi Anda terpengaruh, cara membangun ulang aplikasi (jika berlaku), dan cara menguji aplikasi Anda di lingkungan 16 KB menggunakan emulator (termasuk image sistem Android 15 untuk Android Emulator).
Manfaat dan peningkatan performa
Perangkat yang dikonfigurasi dengan ukuran halaman 16 KB menggunakan memori yang sedikit lebih banyak secara rata-rata, tetapi juga mendapatkan berbagai peningkatan performa untuk sistem dan aplikasi:
- Waktu peluncuran aplikasi lebih rendah saat sistem berada dalam tekanan memori: rata-rata 3,16% lebih rendah, dengan peningkatan yang lebih signifikan (hingga 30%) untuk beberapa aplikasi yang kami uji
- Mengurangi penggunaan daya selama peluncuran aplikasi: Pengurangan rata-rata 4,56%
- Peluncuran kamera lebih cepat: rata-rata hot start 4,48% lebih cepat dan cold start 6,60% lebih cepat
- Waktu booting sistem yang lebih baik: rata-rata meningkat sebesar 8% (sekitar 950 milidetik)
Peningkatan ini didasarkan pada pengujian awal kami, dan hasil pada perangkat aktual kemungkinan akan berbeda. Kami akan memberikan analisis tambahan tentang potensi keuntungan untuk aplikasi saat kami melanjutkan pengujian.
Periksa apakah aplikasi Anda terpengaruh
Jika aplikasi Anda menggunakan kode native, Anda harus membangun ulang aplikasi dengan dukungan untuk perangkat 16 KB. Jika tidak yakin apakah aplikasi Anda menggunakan kode native atau tidak, Anda dapat menggunakan APK Analyzer untuk mengidentifikasi apakah ada kode native atau tidak, lalu memeriksa perataan segmen ELF untuk library bersama yang Anda temukan. Android Studio juga menyediakan fitur yang membantu Anda mendeteksi masalah perataan secara otomatis.
Jika aplikasi Anda hanya menggunakan kode yang ditulis dalam bahasa pemrograman Java atau di Kotlin, termasuk semua library atau SDK, berarti aplikasi Anda sudah mendukung perangkat 16 KB. Namun, sebaiknya Anda menguji aplikasi di lingkungan 16 KB untuk memverifikasi bahwa tidak ada regresi perilaku aplikasi yang tidak terduga.
Perubahan yang diperlukan agar beberapa aplikasi mendukung ruang privasi
Ruang privasi adalah fitur baru di Android 15 yang memungkinkan pengguna membuat ruang terpisah di perangkat mereka tempat mereka dapat menjaga aplikasi sensitif agar tidak dilihat orang lain, di bawah lapisan autentikasi tambahan. Karena aplikasi di ruang pribadi memiliki visibilitas terbatas, beberapa jenis aplikasi perlu mengambil langkah tambahan agar dapat melihat dan berinteraksi dengan aplikasi di ruang pribadi pengguna.
Semua aplikasi
Karena aplikasi di ruang pribadi disimpan dalam profil pengguna terpisah, mirip dengan profil kerja, aplikasi tidak boleh mengasumsikan bahwa salinan aplikasi yang diinstal yang tidak ada di profil utama berada di profil kerja. Jika aplikasi Anda memiliki logika yang terkait dengan aplikasi profil kerja yang membuat asumsi ini, Anda harus menyesuaikan logika ini.
Aplikasi medis
Saat pengguna mengunci ruang pribadi, semua aplikasi di ruang pribadi akan dihentikan, dan aplikasi tersebut tidak dapat melakukan aktivitas latar depan atau latar belakang, termasuk menampilkan notifikasi. Perilaku ini dapat berdampak signifikan pada penggunaan dan fungsi aplikasi medis yang diinstal di ruang privasi.
Pengalaman penyiapan ruang privasi memperingatkan pengguna bahwa ruang privasi tidak cocok untuk aplikasi yang perlu melakukan aktivitas latar depan atau latar belakang penting, seperti menampilkan notifikasi dari aplikasi medis. Namun, aplikasi tidak dapat menentukan apakah aplikasi tersebut digunakan di ruang pribadi atau tidak, sehingga aplikasi tidak dapat menampilkan peringatan kepada pengguna untuk kasus ini.
Karena alasan ini, jika Anda mengembangkan aplikasi medis, tinjau pengaruh fitur ini terhadap aplikasi Anda dan ambil tindakan yang sesuai—seperti memberi tahu pengguna untuk tidak menginstal aplikasi Anda di ruang pribadi—untuk menghindari gangguan pada kemampuan aplikasi yang penting.
Aplikasi peluncur
Jika mengembangkan aplikasi peluncur, Anda harus melakukan hal berikut sebelum aplikasi di ruang pribadi dapat dilihat:
- Aplikasi Anda harus ditetapkan sebagai aplikasi peluncur default untuk perangkat, yaitu
memiliki peran
ROLE_HOME. - Aplikasi Anda harus mendeklarasikan izin normal
ACCESS_HIDDEN_PROFILESdi file manifes aplikasi Anda.
Aplikasi peluncur yang mendeklarasikan izin ACCESS_HIDDEN_PROFILES harus menangani
kasus penggunaan ruang pribadi berikut:
- Aplikasi Anda harus memiliki penampung peluncur terpisah untuk aplikasi yang diinstal di
ruang pribadi. Gunakan metode
getLauncherUserInfo()untuk menentukan jenis profil pengguna yang ditangani. - Pengguna harus dapat menyembunyikan dan menampilkan penampung ruang pribadi.
- Pengguna harus dapat mengunci dan membuka kunci penampung ruang pribadi. Gunakan
metode
requestQuietModeEnabled()untuk mengunci (dengan meneruskantrue) atau membuka kunci (dengan meneruskanfalse) ruang pribadi. Saat terkunci, tidak ada aplikasi di penampung ruang pribadi yang dapat dilihat atau ditemukan melalui mekanisme seperti penelusuran. Aplikasi Anda harus mendaftarkan penerima untuk siaran
ACTION_PROFILE_AVAILABLEdanACTION_PROFILE_UNAVAILABLEserta memperbarui UI di aplikasi Anda saat status penampung ruang pribadi terkunci atau tidak terkunci berubah. Kedua siaran ini menyertakanEXTRA_USER, yang dapat digunakan aplikasi Anda untuk merujuk ke pengguna profil pribadi.Anda juga dapat menggunakan metode
isQuietModeEnabled()untuk memeriksa apakah profil ruang pribadi terkunci atau tidak.
Aplikasi app store
Ruang pribadi menyertakan tombol "Instal Aplikasi" yang meluncurkan intent implisit
untuk menginstal aplikasi ke ruang pribadi pengguna. Agar aplikasi Anda
menerima intent implisit ini, deklarasikan <intent-filter>
dalam file manifes aplikasi dengan <category> dari
CATEGORY_APP_MARKET.
Font emoji berbasis PNG dihapus
File font emoji lama berbasis PNG (NotoColorEmojiLegacy.ttf) telah
dihapus, sehingga hanya menyisakan file berbasis vektor. Mulai Android 13 (API
level 33), file font emoji yang digunakan oleh perender emoji sistem berubah dari
file berbasis PNG menjadi file berbasis vektor. Sistem mempertahankan
file font lama di Android 13 dan 14 karena alasan kompatibilitas, sehingga
aplikasi dengan perender fontnya sendiri dapat terus menggunakan file font lama
hingga dapat diupgrade.
Untuk memeriksa apakah aplikasi Anda terpengaruh, telusuri kode aplikasi Anda untuk menemukan referensi ke
file NotoColorEmojiLegacy.ttf.
Anda dapat memilih untuk menyesuaikan aplikasi dengan beberapa cara:
- Gunakan API platform untuk rendering teks. Anda dapat merender teks ke
Canvasyang didukung bitmap dan menggunakannya untuk mendapatkan gambar mentah jika diperlukan. - Tambahkan dukungan font COLRv1 ke aplikasi Anda. Library open source FreeType mendukung COLRv1 dalam versi 2.13.0 dan yang lebih tinggi.
- Sebagai upaya terakhir, Anda dapat memaketkan file font emoji lama
(
NotoColorEmoji.ttf) ke dalam APK, meskipun dalam hal ini aplikasi Anda akan kehilangan update emoji terbaru. Untuk mengetahui informasi selengkapnya, lihat halaman project GitHub Noto Emoji.
Meningkatkan versi SDK target minimum dari 23 menjadi 24
Android 15 dibuat berdasarkan
perubahan yang dibuat di Android 14 dan memperluasnya
keamanan lebih lanjut. Di Android 15, aplikasi dengan
targetSdkVersion yang lebih rendah dari 24 tidak dapat diinstal.
Mewajibkan aplikasi memenuhi API level modern membantu memastikan keamanan dan
privasi.
Malware sering kali menargetkan API level yang lebih rendah untuk mengabaikan keamanan dan privasi
yang telah diperkenalkan di versi
Android yang lebih tinggi. Misalnya,
beberapa aplikasi malware menggunakan targetSdkVersion dari 22 agar tidak dikenai
model izin runtime yang diperkenalkan pada tahun 2015 oleh Android 6.0 Marshmallow (API
level 23). Perubahan Android 15 ini mempersulit malware untuk menghindari keamanan
dan peningkatan privasi. Mencoba menginstal aplikasi yang menargetkan API yang lebih rendah
tingkat yang mengakibatkan kegagalan instalasi, dengan pesan seperti berikut
muncul di Logcat:
INSTALL_FAILED_DEPRECATED_SDK_VERSION: App package must target at least SDK version 24, but found 7
Pada perangkat yang diupgrade ke Android 15, aplikasi apa pun dengan targetSdkVersion lebih rendah
dari 24 unit organisasi yang
tetap terinstal.
Jika Anda perlu menguji aplikasi yang menargetkan API level lama, gunakan perintah ADB berikut:
adb install --bypass-low-target-sdk-block FILENAME.apk
Keamanan dan privasi
Android 15 memperkenalkan langkah-langkah andal untuk memerangi penipuan kode sandi sekali pakai (OTP) dan untuk melindungi konten sensitif pengguna, dengan berfokus pada hardening Layanan Pemroses Notifikasi dan perlindungan berbagi layar. Peningkatan utama meliputi menyamarkan OTP dari notifikasi yang dapat diakses oleh aplikasi yang tidak tepercaya, menyembunyikan notifikasi selama berbagi layar, dan mengamankan aktivitas aplikasi saat OTP diposting. Perubahan ini bertujuan untuk menjaga konten sensitif pengguna agar aman dari pelaku yang tidak sah.
Developer harus mengetahui hal berikut untuk memastikan aplikasi mereka kompatibel dengan perubahan di Android 15:
Penyamaran OTP
Android akan menghentikan aplikasi tidak tepercaya yang menerapkan
NotificationListenerService agar tidak membaca konten yang tidak disamarkan
dari notifikasi tempat OTP telah terdeteksi. Aplikasi tepercaya seperti
asosiasi pengelola perangkat pendamping dikecualikan dari batasan ini.
Perlindungan Berbagi Layar
- Konten notifikasi disembunyikan selama sesi berbagi layar untuk menjaga
privasi pengguna. Jika aplikasi menerapkan
setPublicVersion(), Android akan menampilkan versi publik notifikasi yang berfungsi sebagai notifikasi pengganti dalam konteks yang tidak aman. Jika tidak, konten notifikasi akan disamarkan tanpa konteks lebih lanjut. - Konten sensitif seperti input sandi disembunyikan dari penonton jarak jauh untuk mencegah pengungkapan informasi sensitif pengguna.
- Aktivitas dari aplikasi yang memposting notifikasi selama berbagi layar saat OTP telah terdeteksi akan disembunyikan. Konten aplikasi disembunyikan dari penampil jarak jauh saat diluncurkan.
- Selain identifikasi otomatis Android terhadap kolom sensitif, developer
dapat menandai bagian aplikasi mereka sebagai sensitif secara manual menggunakan
setContentSensitivity, yang disembunyikan dari penonton jarak jauh selama berbagi layar. - Developer dapat memilih untuk mengalihkan opsi Nonaktifkan perlindungan berbagi layar di bagian Opsi Developer agar dikecualikan dari perlindungan berbagi layar untuk tujuan demo atau pengujian. Perekam layar sistem default dikecualikan dari perubahan ini, karena rekaman tetap berada di perangkat.
Kamera dan media
Android 15 membuat perubahan berikut pada perilaku kamera dan media untuk semua aplikasi.
Pemutaran audio langsung dan pelepasan membatalkan trek audio langsung atau pelepasan yang dibuka sebelumnya saat batas resource tercapai
Sebelum Android 15, jika aplikasi meminta pemutaran audio langsung atau offload saat
aplikasi lain memutar audio dan batas resource tercapai, aplikasi
akan gagal membuka AudioTrack baru.
Mulai Android 15, saat aplikasi meminta pemutaran langsung atau
pemuatan dan batas
resource tercapai, sistem akan membatalkan objek
AudioTrack yang saat ini terbuka yang mencegah pemenuhan permintaan trek baru.
(Jalur audio langsung dan offload biasanya dibuka untuk pemutaran format audio terkompresi. Kasus penggunaan umum untuk memutar audio langsung mencakup streaming audio yang dienkode melalui HDMI ke TV. Jalur offload biasanya digunakan untuk memutar audio yang dikompresi di perangkat seluler dengan akselerasi DSP hardware.)
Pengalaman pengguna dan UI sistem
Android 15 menyertakan beberapa perubahan yang dimaksudkan untuk menciptakan pengalaman pengguna yang lebih konsisten dan intuitif.
Animasi kembali prediktif diaktifkan untuk aplikasi yang memilih ikut serta
Mulai Android 15, opsi developer untuk animasi kembali prediktif telah dihapus. Animasi sistem seperti kembali ke layar utama, lintas tugas, dan lintas aktivitas kini muncul untuk aplikasi yang telah mengaktifkan gestur kembali prediktif secara keseluruhan atau di tingkat aktivitas. Jika aplikasi Anda terpengaruh, lakukan tindakan berikut:
- Pastikan aplikasi Anda telah dimigrasikan dengan benar untuk menggunakan gestur kembali prediktif.
- Pastikan transisi fragmen Anda berfungsi dengan navigasi kembali prediktif.
- Bermigrasi dari animasi dan transisi framework, lalu gunakan transisi animator dan androidx.
- Bermigrasi dari data sebelumnya yang tidak diketahui
FragmentManager. Gunakan data sebelumnya yang dikelola olehFragmentManageratau oleh komponen Navigasi.
Widget dinonaktifkan saat pengguna menghentikan aplikasi secara paksa
Jika pengguna menghentikan paksa aplikasi di perangkat yang menjalankan Android 15, sistem akan menonaktifkan semua widget aplikasi untuk sementara. Widget berwarna abu-abu, dan pengguna tidak dapat berinteraksi dengannya. Hal ini karena mulai Android 15, sistem akan membatalkan semua intent yang tertunda aplikasi saat aplikasi dipaksa berhenti.
Sistem akan mengaktifkan kembali widget tersebut saat pengguna meluncurkan aplikasi lagi.
Untuk informasi selengkapnya, lihat Perubahan pada status paket dihentikan.
Chip status bar proyeksi media memberi tahu pengguna tentang berbagi layar, transmisi, dan perekaman
Screen projection exploits expose private user data such as financial information because users don't realize their device screen is being shared.
For apps running on devices with Android 15 QPR1 or higher, a status bar chip that is large and prominent alerts users to any in‑progress screen projection. Users can tap the chip to stop their screen from being shared, cast, or recorded. Also, screen projection automatically stops when the device screen is locked.
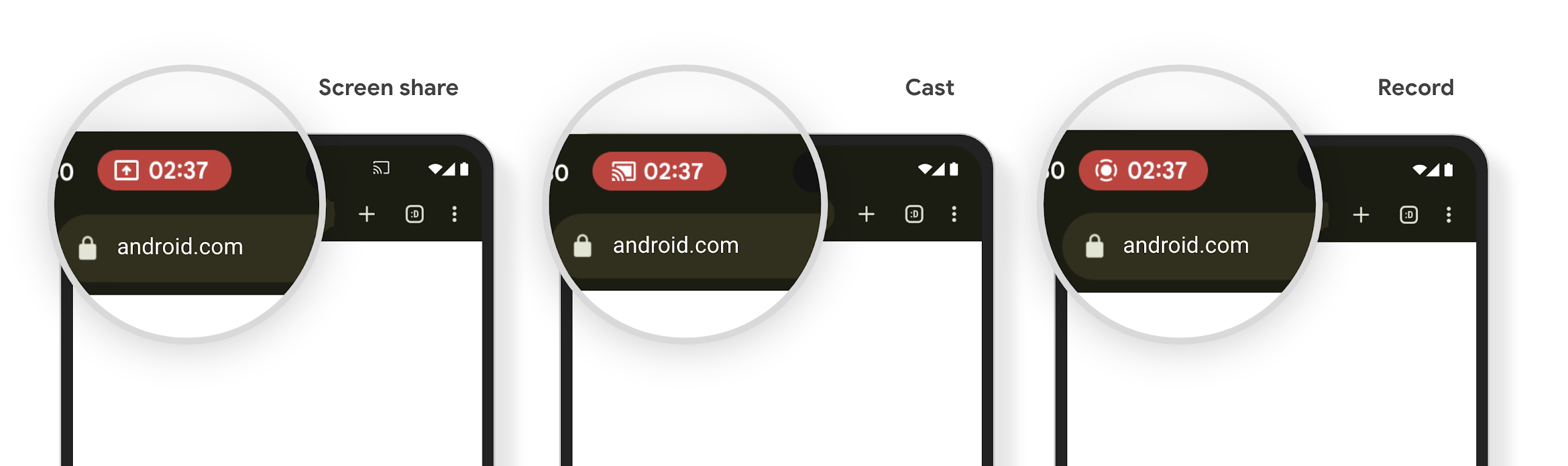
Periksa apakah aplikasi Anda terpengaruh
Secara default, aplikasi Anda menyertakan chip status bar dan otomatis menangguhkan proyeksi layar saat layar kunci diaktifkan.
Untuk mempelajari lebih lanjut cara menguji aplikasi Anda untuk kasus penggunaan ini, lihat Chip status bar dan berhenti otomatis.
Pembatasan akses jaringan di latar belakang
Di Android 15, aplikasi yang memulai permintaan jaringan di luar siklus proses yang valid akan menerima pengecualian. Biasanya, UnknownHostException atau IOException
terkait soket lainnya. Permintaan jaringan yang terjadi di luar siklus proses yang valid
biasanya karena aplikasi tidak sengaja melanjutkan permintaan jaringan bahkan setelah aplikasi
tidak lagi aktif.
Untuk mengurangi pengecualian ini, pastikan permintaan jaringan Anda berbasis siklus proses dan dibatalkan setelah keluar dari siklus proses yang valid dengan menggunakan komponen berbasis siklus proses. Jika permintaan jaringan harus terjadi meskipun pengguna keluar dari aplikasi, pertimbangkan untuk menjadwalkan permintaan jaringan menggunakan WorkManager atau melanjutkan tugas yang terlihat pengguna menggunakan Layanan Latar Depan.
Penghentian penggunaan
Dengan setiap rilis, API Android tertentu mungkin tidak digunakan lagi atau harus difaktorkan ulang untuk memberikan pengalaman developer yang lebih baik atau mendukung kemampuan platform baru. Dalam kasus ini, kami secara resmi menghentikan penggunaan API yang tidak digunakan lagi dan mengarahkan developer ke API alternatif yang akan digunakan.
Penghentian berarti bahwa kami telah mengakhiri dukungan resmi untuk API, tetapi akan tetap tersedia bagi developer. Untuk mempelajari lebih lanjut penghentian penggunaan penting dalam rilis Android ini, lihat halaman penghentian penggunaan.
