Android 15 platformu, uygulamanızı etkileyebilecek davranış değişiklikleri içerir.
Aşağıdaki davranış değişiklikleri, targetSdkVersion'den bağımsız olarak Android 15'te çalıştırıldığında tüm uygulamalar için geçerlidir. Uygulamanızı test etmeli ve ardından, uygun olduğu durumlarda bunları düzgün şekilde desteklemek için gerektiği gibi değiştirmelisiniz.
Yalnızca Android 15'i hedefleyen uygulamaları etkileyen davranış değişiklikleri listesini de incelemeyi unutmayın.
Temel işlevler
Android 15, Android sisteminin çeşitli temel özelliklerini değiştirir veya genişletir.
Paketin durdurulmuş durumunda yapılan değişiklikler
Paket FLAG_STOPPED durumunun amacı (kullanıcı AOSP derlemelerinde bir uygulama simgesine uzun basıp "Zorla Durdur"u seçerek bu işleme başlayabilir), kullanıcı uygulamayı doğrudan başlatarak veya dolaylı olarak uygulamayla etkileşime geçerek (paylaşım sayfası veya widget aracılığıyla, uygulamayı canlı duvar kağıdı olarak seçerek vb.) uygulamayı bu durumdan açıkça kaldırana kadar uygulamaları bu durumda tutmak olmuştur. Android 15'te, sistemin davranışını bu amaçlanan davranışla uyumlu olacak şekilde güncelledik. Uygulamalar yalnızca doğrudan veya dolaylı kullanıcı işlemiyle durdurulmuş durumundan kaldırılmalıdır.
Sistem, istenen davranışı desteklemek için Android 15 çalıştıran bir cihazda uygulama durdurulmuş duruma girdiğinde mevcut kısıtlamalara ek olarak tüm beklemedeki intent'leri de iptal eder. Kullanıcının işlemleri uygulamayı durdurulmuş durumdan çıkardığında ACTION_BOOT_COMPLETED yayını uygulamaya gönderilir. Bu yayın, bekleyen tüm intent'leri yeniden kaydetme fırsatı sunar.
Uygulamanın durdurulmuş duruma alınıp alınmadığını onaylamak için yeni ApplicationStartInfo.wasForceStopped() yöntemini çağırabilirsiniz.
16 KB sayfa boyutları için destek
Android, geçmişte yalnızca 4 KB bellek sayfası boyutlarını desteklemişti. Bu da Android cihazların genellikle sahip olduğu toplam bellek miktarı için sistem belleği performansını optimize etmişti. Android 15'ten itibaren AOSP, 16 KB sayfa boyutu kullanacak şekilde yapılandırılmış cihazları (16 KB cihazlar) destekler. Uygulamanız doğrudan veya bir SDK üzerinden dolaylı olarak NDK kitaplıkları kullanıyorsa uygulamanızı 16 KB'lık cihazlarda çalışacak şekilde yeniden oluşturmanız gerekir.
Cihaz üreticileri daha fazla fiziksel bellek (RAM) içeren cihazlar üretmeye devam ettikçe bu cihazların çoğu, cihazın performansını optimize etmek için 16 KB (ve sonunda daha büyük) sayfa boyutlarını kullanacak. 16 KB sayfa boyutuna sahip cihazlar için destek eklemek, uygulamanızın bu cihazlarda çalışmasını sağlar ve uygulamanızın ilgili performans iyileştirmelerinden yararlanmasına yardımcı olur. Yeniden derlenmeyen uygulamalar, gelecekteki Android sürümlerinde 16 KB'lık cihazlarda çalışmayacaktır.
Uygulamanıza destek eklemenize yardımcı olmak için uygulamanızın etkilenip etkilenmediğini kontrol etme, uygulamanızı yeniden oluşturma (geçerliyse) ve emülatörleri (Android Emulator için Android 15 sistem görüntüleri dahil) kullanarak uygulamanızı 16 KB ortamında test etme hakkında rehberlik sağladık.
Avantajlar ve performans kazanımları
16 KB sayfa boyutlarıyla yapılandırılan cihazlar, ortalama olarak biraz daha fazla bellek kullanır. Ancak, hem sistem hem de uygulamalar için çeşitli performans iyileştirmeleri sağlar:
- Sistem bellek baskısı altındayken daha düşük uygulama başlatma süreleri: Test ettiğimiz bazı uygulamalarda daha belirgin iyileştirmeler (%30'a varan) ile birlikte ortalama %3, 16 daha düşük
- Uygulama başlatma sırasında güç tüketimi azaltıldı: Ortalama% 4,56 oranında azalma
- Daha hızlı kamera başlatma: Ortalama% 4,48 daha hızlı çalışır durumda başlatma ve ortalama% 6,60 daha hızlı soğuk başlatma
- İyileştirilmiş sistem önyükleme süresi: Ortalama %8 (yaklaşık 950 milisaniye) iyileşme
Bu iyileştirmeler, ilk testlerimizi temel almaktadır ve gerçek cihazlardaki sonuçlar büyük olasılıkla farklılık gösterecektir. Testlerimizi sürdürürken uygulamaların olası kazanımlara ilişkin ek analizler sağlayacağız.
Uygulamanızın etkilenip etkilenmediğini kontrol edin
Uygulamanız yerel kod kullanıyorsa uygulamanızı 16 KB cihazları destekleyecek şekilde yeniden oluşturmanız gerekir. Uygulamanızın yerel kod kullanıp kullanmadığından emin değilseniz APK Analiz Aracı'nı kullanarak yerel kod olup olmadığını belirleyebilir ve ardından bulduğunuz paylaşılan kitaplıklar için ELF segmentlerinin hizalamasını kontrol edebilirsiniz. Android Studio, hizalama sorunlarını otomatik olarak algılamanıza yardımcı olan özellikler de sunar.
Uygulamanızda yalnızca Java programlama dilinde veya Kotlin'de yazılmış kodlar (tüm kitaplıklar veya SDK'lar dahil) kullanılıyorsa uygulamanız 16 KB cihazları zaten destekliyor demektir. Bununla birlikte, uygulama davranışında beklenmedik bir gerileme olmadığını doğrulamak için uygulamanızı 16 KB ortamında test etmenizi öneririz.
Bazı uygulamaların özel alanı desteklemesi için gerekli değişiklikler
Özel alan, Android 15'teki yeni bir özelliktir. Kullanıcıların cihazlarında ayrı bir alan oluşturarak hassas uygulamaları, ek bir kimlik doğrulama katmanıyla meraklı gözlerden korumalarına olanak tanır. Özel alandaki uygulamaların görünürlüğü kısıtlandığından, bazı uygulama türlerinin kullanıcının özel alanındaki uygulamaları görüp bunlarla etkileşim kurabilmesi için ek adımlar atması gerekir.
Tüm uygulamalar
Gizli alandaki uygulamalar, iş profillerine benzer şekilde ayrı bir kullanıcı profilinde tutulduğundan, uygulamaların ana profilde olmayan yüklü kopyalarının iş profilinde olduğunu varsaymaması gerekir. Uygulamanızda, iş profili uygulamalarıyla ilgili bu varsayımı yapan bir mantık varsa bu mantığı düzenlemeniz gerekir.
Tıbbi uygulamalar
Kullanıcı özel alanı kilitlediğinde özel alandaki tüm uygulamalar durdurulur ve bu uygulamalar, bildirim göstermek de dahil olmak üzere ön planda veya arka planda etkinlik gerçekleştiremez. Bu davranış, özel alana yüklenen tıbbi uygulamaların kullanımını ve işlevini önemli ölçüde etkileyebilir.
Özel alan kurulum deneyimi, kullanıcıları özel alanın tıbbi uygulamalardan gelen bildirimleri gösterme gibi kritik ön plan veya arka plan etkinlikleri gerçekleştirmesi gereken uygulamalar için uygun olmadığı konusunda uyarır. Ancak uygulamalar, özel alanda kullanılıp kullanılmadıklarını belirleyemediğinden bu durumda kullanıcıya uyarı gösteremez.
Bu nedenle, tıbbi uygulama geliştiriyorsanız bu özelliğin uygulamanızı nasıl etkileyebileceğini inceleyin ve kritik uygulama özelliklerinin kesintiye uğramasını önlemek için uygun işlemleri yapın (ör. kullanıcılarınızı uygulamanızı özel alana yüklememeleri konusunda bilgilendirin).
Başlatıcı uygulamaları
Bir başlatıcı uygulaması geliştirirseniz özel alandaki uygulamaların görünmesi için aşağıdakileri yapmanız gerekir:
- Uygulamanız, cihaz için varsayılan başlatıcı uygulaması olarak atanmış olmalıdır. Yani
ROLE_HOMErolüne sahip olmalıdır. - Uygulamanız,
ACCESS_HIDDEN_PROFILESnormal iznini uygulamanızın manifest dosyasında beyan etmelidir.
ACCESS_HIDDEN_PROFILES iznini beyan eden başlatıcı uygulamaları aşağıdaki özel alan kullanım alanlarını ele almalıdır:
- Uygulamanızda, özel alana yüklenen uygulamalar için ayrı bir başlatıcı kapsayıcısı olmalıdır. Hangi tür kullanıcı profilinin işlendiğini belirlemek için
getLauncherUserInfo()yöntemini kullanın. - Kullanıcı, özel alan kapsayıcısını gizleyip gösterebilmelidir.
- Kullanıcı, özel alan kapsayıcısını kilitleyip kilidini açabilmelidir. Özel alanı kilitlemek (
trueile) veya kilidini açmak (falseile) içinrequestQuietModeEnabled()yöntemini kullanın. Kilitliyken özel alan kapsayıcısındaki hiçbir uygulama görünmemeli veya arama gibi mekanizmalar aracılığıyla bulunamamalıdır. Uygulamanız,
ACTION_PROFILE_AVAILABLEveACTION_PROFILE_UNAVAILABLEyayınları için bir alıcı kaydettirmeli ve özel alan kapsayıcısının kilitli veya kilidi açık durumu değiştiğinde uygulamanızdaki kullanıcı arayüzünü güncellemelidir. Bu yayınların her ikisi deEXTRA_USERiçerir. Uygulamanız, özel profil kullanıcısını belirtmek için bu kimliği kullanabilir.Özel alan profilinin kilitli olup olmadığını kontrol etmek için
isQuietModeEnabled()yöntemini de kullanabilirsiniz.
Uygulama mağazası uygulamaları
Özel alanda, kullanıcının özel alanına uygulama yüklemek için bir örtülü intent başlatan bir "Uygulama Yükle" düğmesi bulunur. Uygulamanızın bu dolaylı intent'i alabilmesi için uygulamanızın manifest dosyasında CATEGORY_APP_MARKET <category> içeren bir <intent-filter> beyan edin.
PNG tabanlı emoji yazı tipi kaldırıldı
Eski, PNG tabanlı emoji yazı tipi dosyası (NotoColorEmojiLegacy.ttf) kaldırıldı ve yalnızca vektör tabanlı dosya kaldı. Android 13'ten (API düzeyi 33) itibaren sistem emoji oluşturma aracı tarafından kullanılan emoji yazı tipi dosyası PNG tabanlı bir dosyadan vektör tabanlı bir dosyaya değiştirildi. Sistem, Android 13 ve 14'te uyumluluk nedeniyle eski yazı tipi dosyasını sakladı. Böylece, kendi yazı tipi oluşturma araçlarına sahip uygulamalar yeni sürüme geçene kadar eski yazı tipi dosyasını kullanmaya devam edebildi.
Uygulamanızın etkilenip etkilenmediğini kontrol etmek için uygulamanızın kodunda NotoColorEmojiLegacy.ttf dosyasına yapılan referansları arayın.
Uygulamanızı birkaç şekilde uyarlayabilirsiniz:
- Metin oluşturma için platform API'lerini kullanın. Metni bitmap destekli bir
Canvasolarak oluşturabilir ve gerekirse ham resim elde etmek için bunu kullanabilirsiniz. - Uygulamanıza COLRv1 yazı tipi desteği ekleyin. FreeType açık kaynak kitaplığı, 2.13.0 sürümü ve sonraki sürümlerde COLRv1'i destekler.
- Son çare olarak eski emoji yazı tipi dosyasını (
NotoColorEmoji.ttf) APK'nıza ekleyebilirsiniz. Ancak bu durumda uygulamanızda en son emoji güncellemeleri eksik olur. Daha fazla bilgi için Noto Emoji GitHub proje sayfasına göz atın.
Minimum hedef SDK sürümü 23'ten 24'e yükseltildi
Android 15
Android 14'te yapılan değişiklikler ve bu değişikliğin kapsamını genişleterek
daha fazla güvenlik. Android 15'te targetSdkVersion değeri 24'ten düşük olan uygulamalar yüklenemez.
Uygulamaların modern API seviyelerini karşılamasını zorunlu kılmak, güvenliğin ve
gizlilik.
Kötü amaçlı yazılımlar, güvenlik ve gizliliği atlamak için genellikle daha düşük API seviyelerini hedefler.
yüksek Android sürümlerinde sunulan koruma özellikleri. Örneğin,
bazı kötü amaçlı yazılım uygulamalarıtargetSdkVersion
Android 6.0 Marshmallow (API) tarafından 2015'te kullanıma sunulan çalışma zamanı izin modeli
23. düzey). Android 15'teki bu değişiklik, kötü amaçlı yazılımların güvenlikten kaçınmasını zorlaştırıyor
ve gizlilikle ilgili iyileştirmeler yapıldı. Daha düşük bir API'yi hedefleyen bir uygulama yüklenmeye çalışılıyor
düzeyinde bir yükleme işlemi hatasıyla sonuçlanır ve bu hataya aşağıdaki gibi bir mesaj gönderilir
Logcat'te görünüyor:
INSTALL_FAILED_DEPRECATED_SDK_VERSION: App package must target at least SDK version 24, but found 7
Android 15'e geçen cihazlarda, targetSdkVersion daha düşük
24'ten fazlası yüklü durumda.
Eski bir API düzeyini hedefleyen bir uygulamayı test etmeniz gerekirse aşağıdaki ADB'yi kullanın komut:
adb install --bypass-low-target-sdk-block FILENAME.apk
Güvenlik ve gizlilik
Android 15, tek kullanımlık şifre kodu (OTP) sahtekarlığıyla mücadele etmek ve kullanıcının hassas içeriklerini korumak için Notification Listener Hizmeti ile ekran paylaşımı korumalarını güçlendirmeye odaklanan güçlü önlemler sunar. Önemli iyileştirmeler arasında, güvenilmeyen uygulamaların erişebildiği bildirimlerden tek kullanımlık şifreleri çıkarma, ekran paylaşımı sırasında bildirimleri gizleme ve tek kullanımlık şifreler yayınlandığında uygulama etkinliklerini güvence altına alma yer alır. Bu değişikliklerin amacı, kullanıcının hassas içeriğini yetkisiz kişilerden korumaktır.
Geliştiricilerin, uygulamalarının Android 15'teki değişikliklerle uyumlu olmasını sağlamak için aşağıdakileri göz önünde bulundurması gerekir:
OTP Çıkarma
Android, NotificationListenerService uygulayan güvenilmeyen uygulamaların, tek kullanımlık şifrenin algılandığı bildirimlerdeki düzeltilmemiş içeriği okumasını engeller. Eşlik eden cihaz yöneticisi dernekleri gibi güvenilir uygulamalar bu kısıtlamalardan muaftır.
Ekran Paylaşımı Koruması
- Kullanıcı gizliliğini korumak için ekran paylaşımı oturumları sırasında bildirim içeriği gizlenir. Uygulama
setPublicVersion()'u uygularsa Android, güvenli olmayan bağlamlarda yedek bildirim olarak hizmet veren bildirimin herkese açık sürümünü gösterir. Aksi takdirde, bildirim içeriği başka bir bağlam bilgisi olmadan çıkartılır. - Şifre girişi gibi hassas içerikler, kullanıcının hassas bilgilerinin açığa çıkmasını önlemek için uzaktan izleyicilere gösterilmez.
- Ekran paylaşımı sırasında OTP algılanan ve bildirim yayınlayan uygulamalardan gelen etkinlikler gizlenir. Uygulama içeriği, başlatıldığında uzaktan görüntüleyene gösterilmez.
- Android'in hassas alanları otomatik olarak tanımlamasının yanı sıra geliştiriciler, ekran paylaşımı sırasında uzak görüntüleyenlerden gizlenen
setContentSensitivitykullanarak uygulamalarının bölümlerini manuel olarak hassas olarak işaretleyebilir. - Geliştiriciler, demo veya test amacıyla ekran paylaşımı korumalarından muaf olmak için Geliştirici Seçenekleri bölümündeki Ekran paylaşımı korumalarını devre dışı bırak seçeneğini etkinleştirebilir. Varsayılan sistem ekran kaydedici, kayıtlar cihazda kaldığı için bu değişikliklerden muaftır.
Kamera ve medya içerikleri
Android 15, tüm uygulamalarda kamera ve medya davranışıyla ilgili aşağıdaki değişiklikleri yapar.
Doğrudan ve dışa aktarılan ses oynatma, kaynak sınırlarına ulaşıldığında daha önce açılmış doğrudan veya dışa aktarılmış ses parçalarını geçersiz kılar.
Android 15'ten önce, başka bir uygulama ses çalarken bir uygulama doğrudan veya aktarma yoluyla ses çalmayı talep ederse ve kaynak sınırlarına ulaşılırsa uygulama yeni bir AudioTrack açamazdı.
Android 15'ten itibaren, bir uygulama doğrudan oynatma veya aktarma oynatma istediğinde ve kaynak sınırlarına ulaşıldığında sistem, yeni parça isteğinin yerine getirilmesini engelleyen, şu anda açık olan tüm AudioTrack nesnelerini geçersiz kılar.
(Doğrudan ve aktarılan ses parçaları genellikle sıkıştırılmış ses biçimlerinin oynatılması için açılır. Doğrudan ses oynatmanın yaygın kullanım alanları arasında, kodlanmış sesi HDMI üzerinden TV'ye aktarma yer alır. İndirilen parçalar genellikle donanım DSP hızlandırması olan bir mobil cihazda sıkıştırılmış ses oynatmak için kullanılır.)
Kullanıcı deneyimi ve sistem arayüzü
Android 15, daha tutarlı ve sezgisel bir kullanıcı deneyimi oluşturmayı amaçlayan bazı değişiklikler içerir.
Katılmayı tercih eden uygulamalarda tahmine dayalı geri hareketi animasyonları etkinleştirildi
Android 15'ten itibaren tahmine dayalı geri animasyonlar için geliştirici seçeneği kaldırıldı. Ana sayfaya geri gitme, görevler arasında geçiş yapma ve etkinlikler arasında geçiş yapma gibi sistem animasyonları artık tahmini geri hareketini etkinleştiren uygulamalarda tamamen veya etkinlik düzeyinde gösteriliyor. Uygulamanız etkilendiyse aşağıdaki işlemleri yapın:
- Uygulamanızın, tahmini geri hareketi kullanacak şekilde düzgün bir şekilde taşındığından emin olun.
- Parça geçişlerinizin tahmini geri gezinme ile çalıştığından emin olun.
- Animasyon ve çerçeve geçişlerinden uzaklaşın ve bunun yerine animatör ve androidx geçişlerini kullanın.
FragmentManager'nin bilmediği arka yığınlardan taşının. Bunun yerineFragmentManagerveya Gezinme bileşeni tarafından yönetilen geri yığınları kullanın.
Kullanıcı bir uygulamayı durdurmaya zorladığında widget'lar devre dışı bırakılıyor
Bir kullanıcı, Android 15 çalıştıran bir cihazda bir uygulamayı zorla durdurursa sistem, uygulamanın tüm widget'larını geçici olarak devre dışı bırakır. Widget'lar devre dışıdır ve kullanıcı bunlarla etkileşim kuramaz. Bunun nedeni, Android 15'ten itibaren sistemin, uygulama zorla durdurulduğunda uygulamanın bekleyen tüm intent'lerini iptal etmesidir.
Sistem, kullanıcı uygulamayı bir sonraki sefer başlattığında bu widget'ları yeniden etkinleştirir.
Daha fazla bilgi için Paket durduruldu durumunda yapılan değişiklikler başlıklı makaleyi inceleyin.
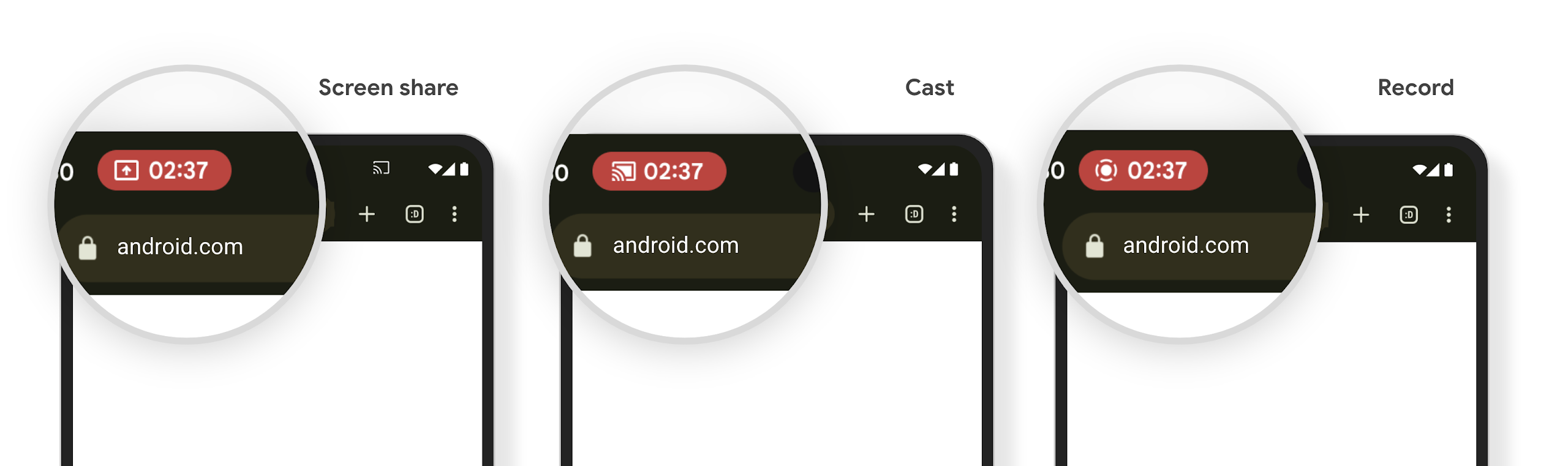
Medya yansıtma durum çubuğu çipi, kullanıcıları ekran paylaşımı, yayınlama ve kayıt konusunda uyarır.
Ekran yansıtma istismarlarında, kullanıcılar cihaz ekranlarının paylaşıldığını fark etmediğinden finansal bilgiler gibi gizli kullanıcı verileri açığa çıkar.
Android 15 QPR1 veya sonraki sürümleri çalıştıran cihazlarda, büyük ve belirgin bir durum çubuğu çipi, devam eden ekran yansıtma işlemleri hakkında kullanıcıları uyarır. Kullanıcılar, ekranlarının paylaşılmasını, yayınlamasını veya kaydedilmesini durdurmak için çipe dokunabilir. Ayrıca, cihaz ekranı kilitlendiğinde ekran yansıtma otomatik olarak durur.
Uygulamanızın etkilenip etkilenmediğini kontrol edin
Uygulamanız varsayılan olarak durum çubuğu çipini içerir ve kilit ekranı etkinleştirildiğinde ekran yansıtmayı otomatik olarak askıya alır.
Uygulamanızı bu kullanım alanları için nasıl test edeceğiniz hakkında daha fazla bilgi edinmek için Durum çubuğu çipi ve otomatik durdurma başlıklı makaleyi inceleyin.
Arka plan ağ erişimi kısıtlamaları
Android 15'te, geçerli bir işlem yaşam döngüsü dışında ağ isteği başlatan uygulamalar istisna alır. Genellikle bir UnknownHostException veya soketle ilgili başka bir IOException olur. Geçerli yaşam döngüsü dışında gerçekleşen ağ istekleri genellikle uygulamaların artık etkin olmasa bile ağ isteklerini bilmeden devam ettirmesinden kaynaklanır.
Bu istisnayı azaltmak için yaşam döngüsü bilincine sahip bileşenler kullanarak ağ isteklerinizin yaşam döngüsü bilincine sahip olduğundan ve geçerli bir işlem yaşam döngüsünden çıktığında iptal edildiğinden emin olun. Ağ isteğinin, kullanıcı uygulamadan ayrılsa bile yapılması önemliyse WorkManager'ı kullanarak ağ isteğini planlayabilir veya ön plan hizmetini kullanarak kullanıcı tarafından görülebilen bir göreve devam edebilirsiniz.
Kullanımdan Kaldırmalar
Her sürümde belirli Android API'leri eski hale gelebilir veya daha iyi bir geliştirici deneyimi sunmak ya da yeni platform özelliklerini desteklemek için yeniden düzenlenmesi gerekebilir. Bu tür durumlarda, eski API'lerin desteğini resmi olarak sonlandırırız ve geliştiricileri bunun yerine kullanabilecekleri alternatif API'lere yönlendiririz.
Desteğin sonlandırılması, API'ler için resmi desteğin sona erdirildiği ancak geliştiricilerin bu API'leri kullanmaya devam edebileceği anlamına gelir. Android'in bu sürümündeki önemli desteği sonlandırılan özellikler hakkında daha fazla bilgi edinmek için desteği sonlandırılan özellikler sayfasını inceleyin.

